Connect up to Five Microsoft 365 Tenants in a Multi-Tenant Organization for Richer Collaboration
When Microsoft introduced shared channels for Teams in 2022, they also introduced Azure B2B Direct Connect, a method of connecting tenants together in a mutual trust arrangement. Cross-tenant access policies are the underpinning of the mutual trust between tenants. As the name suggests, the name dictates how tenants access each other’s resources. Cross-tenant synchronization is another capability controlled by cross-tenant access policies. In this case, it’s to define a trust relationship to synchronize directory objects between tenants.
Now Microsoft has multi-tenant organizations, a new Entra ID solution that’s available in preview. A multi-tenant organization (or MTO) is a set of up to five Entra ID tenants connected together by cross-tenant access policies to make directory synchronization seamless. The solution is directed at organizations that span multiple Microsoft 365 tenants that want to share a common directory and make it easier for users in the connected tenants to share information.
For now, the benefits of easier collaboration only extend to the new Teams 2.1 client, where Microsoft says that users:
- Receive real-time notifications from all tenants in the MTO.
- Don’t need to switch tenants before they can collaborate (chat, call, meet) with users in other MTO tenants. Teams supports federated chat with external people from other tenants. In an MTO, users from the tenants in the MTO are no longer considered external, so full chat features are available.
- Can set a separate status in each tenant.
In addition, the Microsoft 365 user profile card shows the organization name of a user. The Microsoft Teams development group’s blog gives more information about “seamless collaboration in Teams in a multi-tenant organization.”
When generally available, users participating in MTOs will require Entra ID Premium P1 licenses. Given that this is very much an enterprise play, the license requirement shouldn’t be an issue.
Creating a new Multi-tenant Organization
The structure of an MTO is:
- An owning tenant that creates the MTO. A tenant can only be a member of a single MTO.
- Up to four additional tenants added to the MTO.
- Each tenant connects to the other tenants with a cross-tenant synchronization configuration.
- Each tenant controls what users from their directory synchronizes with the other tenants.
- A maximum of up to 100,000 users can synchronize from one tenant to another.
- Tenants can leave an MTO at any time. The MTO is removed when the owning tenant leaves it.
Because this is currently a preview feature, only tenants configured for targeted release can participate in an MTO.
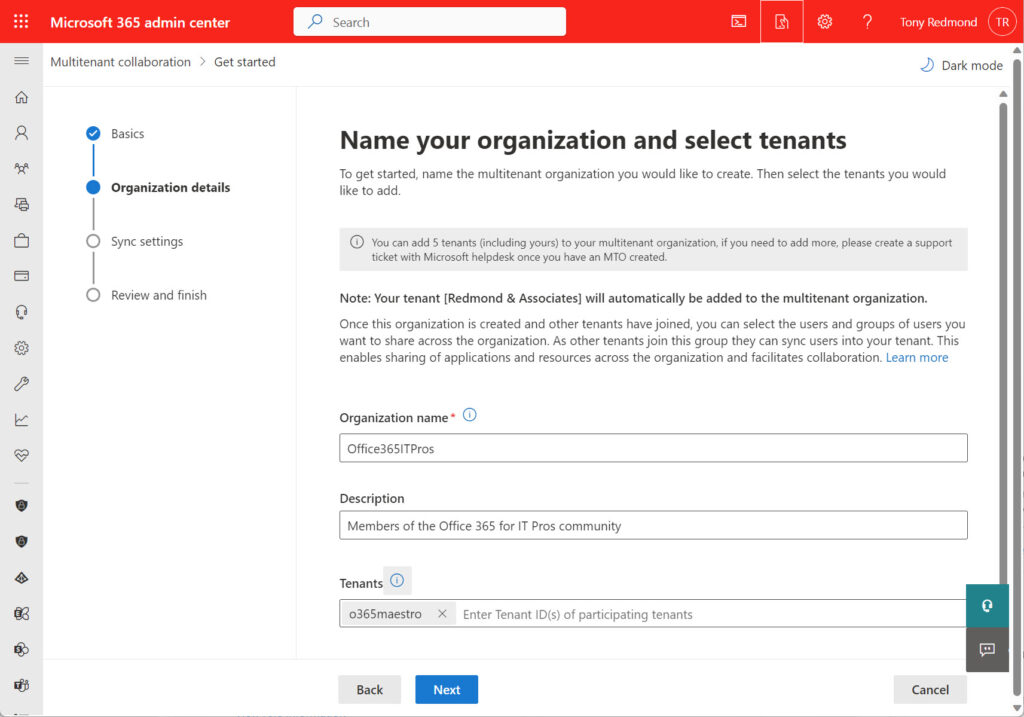
To create a new MTO, go to the Org Settings section of the Microsoft 365 admin center and select the Organization profile tab. Choose Multitenant collaboration to create a new MTO. You can then enter the name of the new MTO, a description, and the tenant identifiers (GUIDs) for the member tenants. I chose to start by connecting with a single tenant (Figure 1).
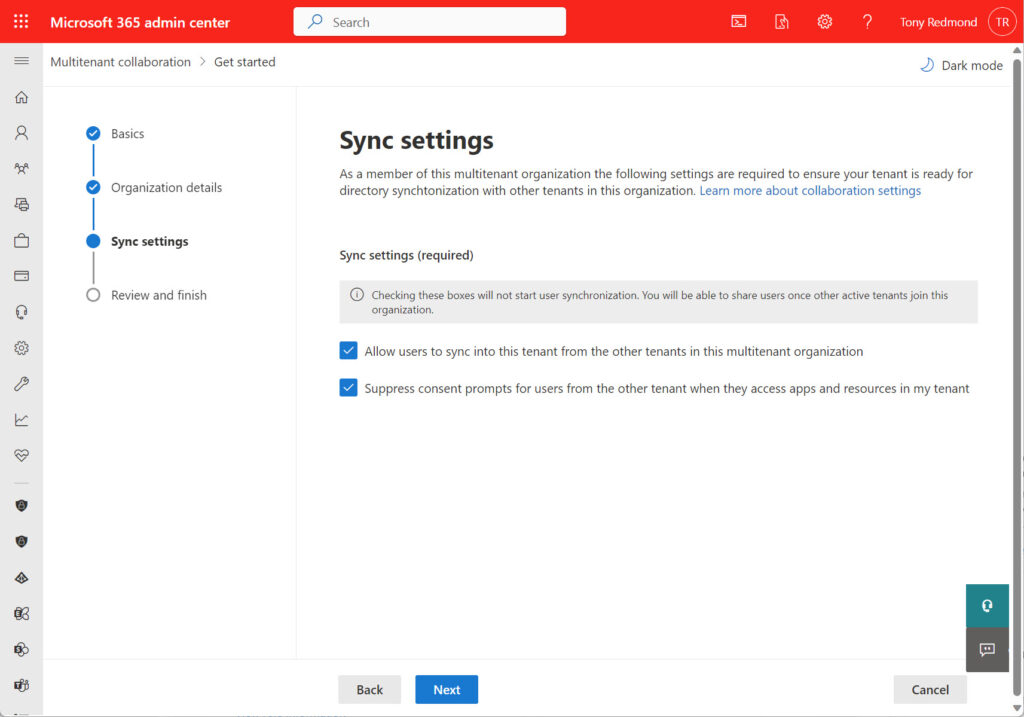
Next, configure the synchronization settings for the connection between the owing tenant and the new member tenant. This is similar to the steps taken to create a cross-tenant synchronization configuration in the Entra ID admin center. The operation is more automated and therefore easier in the Microsoft 365 admin center. The two settings exposed in Figure 2 control user synchronization and suppress consent prompts that users would otherwise have to give to allow their information to be shared through cross-tenant synchronization.
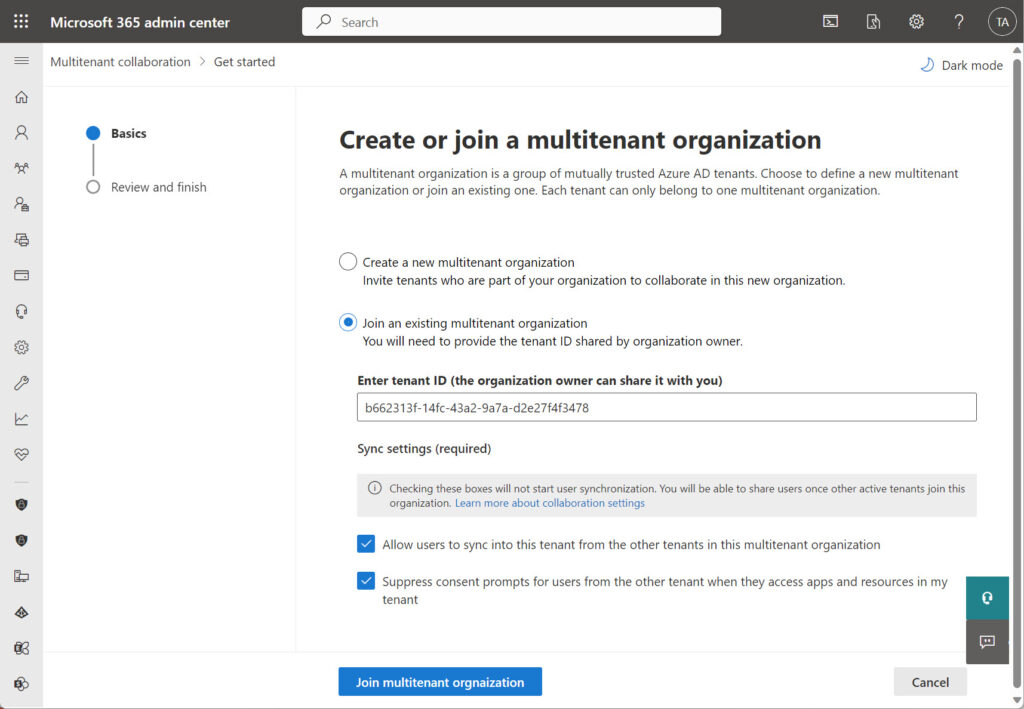
Move to the next screen to review the configuration of the MTO before clicking the big Create multitenant organization to launch the process of populating Entra ID with the necessary properties. This includes preparing the nominated member tenants to join the MTO. However, because tenants operate on a mutual trust arrangement, the administrators of each member tenant must take explicit action to join the MTO. Essentially, this action, executed through the same option in the Microsoft 365 admin center, accepts an invitation from the owner tenant to participate in the MTO (Figure 3).
Entra ID Settings
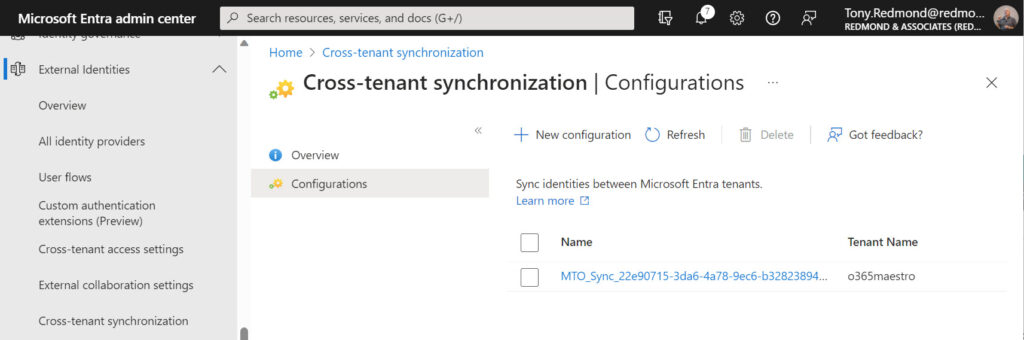
Microsoft 365 makes use of the information synchronized between directories, but Entra ID controls the synchronization. Go to the External Identities section of the Entra ID admin center and you’ll find that a cross-tenant synchronization configuration now exists named MTO_Sync_tenantidentifier (Figure 4)
Configuration settings dictate which users the tenant synchronizes to the other tenant and you can add users and security groups to the configuration to have them synchronize to the other tenant. I found that I had to change the synchronization setting from Manual to Automatic in some tenants, but apart from that, the configuration just worked.
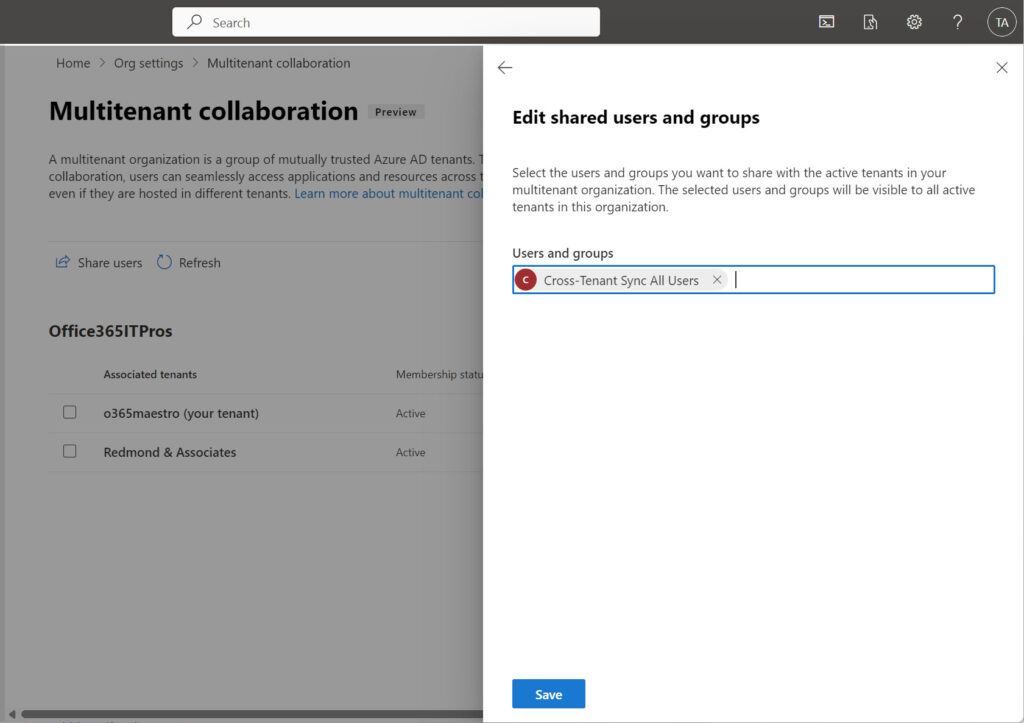
Remember that the MTO is a Microsoft 365 feature built on top of Entra ID, so it’s easier to use the Share users option in the Multitenant collaboration section of the Microsoft 365 admin center to define the users that your tenant is willing to synchronize with all the other tenants in the MTO. In my case, I created a security group and populated it with all the member accounts from the tenant before adding it to the configuration (Figure 5). A dynamic security group also works and is easier to manage in terms of adding new accounts to the synchronize cycle.
If you want control at an individual tenant level (for instance, synchronize some users with one tenant and a different set with another), you can change the provisioning settings of the individual Entra ID configurations for each tenant. Before doing that, reflect that the idea behind the MTO is to have a common directory across the tenants in the MTO. That’s why the default is to synchronize the same users with all tenants.
Members Not Guests
When Entra ID synchronizes accounts from a source tenant to a target tenant, it creates the entries in the target tenant as member accounts, not guest accounts. If you examine the properties of a synchronized account, you can see that the user principal name looks like a guest account but the user type is the same as a regular user account:
Id : 8dd7fdd3-bc6f-4390-ae0a-5910ea577a7d DisplayName : Andy Ruth (Project Director) UserPrincipalName : Andy.Ruth_office365itpros.com#EXT#@o365maestro.onmicrosoft.com Mail : Andy.Ruth@office365itpros.com UserType : Member
Creating synchronized accounts as members with a specific form of UPN means that apps can easily distinguish accounts from an MTO and treat them differently to guest accounts. Quite how that happens within the new Teams client serves a separate article.
At this point, the synchronized accounts have zero impact on other Microsoft 365 apps like Exchange, Planner, Viva Engage, or SharePoint Online. This might change in the future. From a user perspective, the synchronized accounts appear like other member accounts and can be treated as such.
The Start of the MTO Journey
The new multi-tenant organization is a preview feature. As such, we can expect that things might change between now and general availability. However, I don’t think the general structure will change and MTOs will work as described based on top of Entra ID cross-tenant synchronization configurations.
What will be interesting in the future is how this solution will affect ISVs that sell cross-tenant directory synchronization products. I think that MTOs remove the need for some of the needs satisfied by these products, so the market will probably shrink. I’m also interested to see how tenant-to-tenant migration vendors adapt to this new influence. Will MTOs replace the need for some tenant-to-tenant migrations or will an MTO be the opening step for others? We shall see.
And then there’s the question of Microsoft 365 apps. Teams has already said how it will take advantage of being able to distinguish between a synchronized user from a tenant within an MTO and other external accounts. We’ll have to wait and see how Outlook, Viva Engage, Planner, and other apps change, if at all. Overall, the MTO is an interesting prospect to contemplate.
For more information about Microsoft 365 multi-tenant organizations, read this article.
On Demand Migration
Migrate all your workloads and Active Directory with one comprehensive Office 365 tenant-to-tenant migration solution.





Hello Tony – long time no see, hope you’re doing great (as always).
Quick question: beside fact that our Tenants users have that External logo beside their name ( I understand the logic behind this), in Chats MTO doesn’t give an option to the Members for uploading files, screen sharing, or to use apps or … pretty much anything except sending goofy gify stuff – can this be overridden? Any settings hidden somewhere … anything?
It’s kind of funny that Guest users have full chat capability while Members are totally restricted. We hoped MTO would give us better than what we had with classic Azure B2B cross tenant config, but we ended up in a frustration.
It sounded so cool in that Microsoft document.
Complain to Microsoft! File a support request and have them check out your tenant setup first (obviously I have no access to it) and if everything is OK and the functionality you want isn’t available, ask the support team to escalate to engineering.
I have successfully screwed up my MTO configuration… easy to do, not so easy to sort out.
You were right, as always. It was the configuration issue. You’re a shrine. Thanks
“Shrine”?
is there any information on how MTO introduced accounts affect MS Secure Score. It appears that Secure Score looks at all users including those synchronized via MTO
Nothing that I have heard of. I imagine this is something that Microsoft would address when MTO becomes generally available.
You state: “If you want control at an individual tenant level (for instance, synchronize some users with one tenant and a different set with another), you can change the provisioning settings of the individual Entra ID configurations for each tenant.”
Is this still accurate now that you’ve dug further into MTO since you wrote this article? I’m wondering if MTO is a good fit for a parent company/subsidiaries structure where the parent company tenant would sync user with each subsidiary tenant, but there is no need for the subsidiary tenants to sync with each other (ie. hub/spoke vs full mesh)
I have not looked at MTO much since. What I would do is use a couple of developer tenants to set up a MTO and test the scenario you envisage. That’s the right way to validate any specific requirement without making changes to a production tenant.
Hello Tony
When is the official release planned for everyone?
Who knows? Only Microsoft can say.
Great article thanks. Would that make accessing users easier (finding Guests) and collaborating in Teams sites better in any way?
The synchronized users aren’t guests. The accounts exist to make it easier for Teams to recognize that they come from a trusted organization. See https://practical365.com/multi-tenant-organizations-value/ for more information.
MTO is for five tenants only ? If I whant to connect like 50 tenants to form a MTO, what should I use then ?
It is unlikely to happen because shared channel & multi-tenant features touch the commercial licensing border of independent 365 org licenses. That’s why shared channels are limited when sharing with external people and guests.
Connecting 50 tenants appear to have org design issue. You may redesign your organisation to live within limits & ecosystem or consider another platform that aligns with your expectations.
There is a process to increase the limits of having more than 100k users in a tenant or to add more than 5 tenants in an MTO. Open a ticket with support AND allow ample time for Microsoft to put the change through their internal approval process and consequently roll-out to the global environment.
I’m not sure what the level of pushback is when you actually want to do this for 50 tenants, but I have experience with the exception process to allow this for a tenant with more than 100k users.
Always remembering that there’s a reason why the limitations exist while MTO is in beta…
How would licensing work for the various functions, would a person/user need to be licensed per tenant? Would a sync pull in that person as a member with licenses from the setup of the “home” tenant?
You can assign licenses to synchronized member accounts if you really want to, but there’s no need. The synchronized accounts are not there to be used by humans.
this is not always the case. Example: in a typical Cross Tenant setup, John from Tenant A sends a Power Automate approval to Jane in Tenant B. Jane is a guest in Tenant A, and as such does not need a Power Automate license to approve because Guests do not require a license for approval.
Now you change to an MTO, Jane is now upgraded to a Member account in Tenant A and is without a license. Jane can no longer approve that approval without explicitedly granting her Member account in Tenant A a license.
That’s an edge case I did not try out because I don’t use Power Automate for much. You should report it to Microsoft so that the issue is escalated to MTO engineering to have them look at what’s happening.
Hi Tony – have you seen anything in the pipeline that will allow an org to have 2 separate O365 Tenants, but use a single domain/MX (e.g. if they want to manage in-region but keep a single domain across the org). I do recall something in the roadmap but seems to have gone quiet.
Mark
Nope. Zero. Nada.
Not with multiple tenants, but consider a multi-geo tenant and/or using Administrative Units.
So, it seems cross tenant sync is just a method to sync attribute and MTO is a complete solution. Is my understanding correct? Cross tenant sync will remain but MTO is a completer solution?
MTO is a complete solution for situations where less than five tenants wish to form an organization based on directory synchronization.
It depends on how you want the communication structure to appear between two organisations, how closely you wish to share the details with each other, and who will own the data in the conversations. In cross-tenants, the conversation is shared between two orgs through shared channels. You need to share each channel.
In a multi-tenant org (MTO), each org owns its data, and the user’s user’s principal name (UPN) reflects the org’s domain. Channels are set up in the tenant’s own teams, so the history (and shared files) would appear only there.
If you invite a vendor to help you with your org for a limited time and during the early stages of trust building, separate would be fine.
If you are working with a strong collaboration for the long term on a specific topic/idea/innovation and share high trust, cross-origin will make sense.
Tenants don’t need to be always external people. You may even structure your big org into several tenants as it suits the communication structure, data sharing and trust levels.
Is that feautere will replace the Cross-tenant synchronization or it’s totally different? Witch is better to enable for a customer with two separated M365 Tenant?
Probably the MTO.
No, they are not. MTO works in a different degree of collaboration than cross-domain. They have a different purpose. You may check my other comment to identify which is suitable for a given situation.
Hey Tony,
Do you know if this does anything to address the synced objects appearing the the Teams address book but being not routable, so when choosing it to message, it sends to the internal tenant object which isnt checked?
Ive raised it with my CSAM and trying to get in touch with the dev team but its slow, its addressed here and a pretty popular issue: https://techcommunity.microsoft.com/t5/microsoft-entra-azure-ad/ms-teams-in-cross-tenant-synchronization/m-p/3913738/emcs_t/S2h8ZW1haWx8dG9waWNfc3Vic2NyaXB0aW9ufExMWFJCSEhHU1E2RkFSfDM5MTM3Mzh8U1VCU0NSSVBUSU9OU3xoSw#M8715
Anything that you could suggest?
The basic issue here is that the original cross-tenant synchronization mechanism wasn’t tailored to support Microsoft 365 apps. The MTO is explicitly engineered to support Microsoft 365, so it looks (from initial tests) that the use objects synchronized to another tenant a) appear in the GAL and b) are routable because their SMTP mail address is valid.
I have same issue but the opposite, external users email addresess showing as #ext# in GAL in the mail field , but in teams its showing the correct email address
Will this allow users from one tenant to log in to computers on another tenant?
I’m playing with the different permutations that come available through the MTO and will publish something soon to document my results.
I guess custom domains stills needs to be unique in each tenant..🤔
Certainly the tenant identifiers need to be unique. But I have not played with custom domains that are duplicated across tenants. That seems like a very bad situation to be in.
This is interesting. I manage two tenants for subsidiary companies that were originally conceived as separately operating entities, but over time have increasingly tried to operate as a single organization.
I set up Cross-Tenant Sync back when it was in preview, and it’s been very helpful in simplifying sharing of OneDrive/SharePoint and some other stuff across tenants.
Alas, I thought it was a panacea until I realized some of the limitations, such as the fact that when creating a M365 group in tenant A, tenant B users can be members but can’t directly access the group mailbox and calendar.
Really hoping that MTO will address issues like this. Otherwise, joining the two tenants is where I’m ultimately headed, a task I do not relish…
Groups support is obviously a good next step for Microsoft to head toward. Remember, MTO is a preview, so things will change…
Do you think the limit of 5 will increased?
Who knows? It’s a preview…
It won’t since the relaxation would have financial impact on Microsoft’s licensing. Please check my other comment
This is not a hard limit, there is an exception process to allow more than 5 tenants. Open a support ticket to start the process…
Are there plans for cross-cloud (GCCH Commercial) support for MTO?
Not that I know of. You could ask your local Microsoft rep.
Would this MTO principle also work in a Hybrid environment?
I believe so. However, I think it will only synchronize cloud-based accounts. On-premises accounts remain under the control of Active Directory and are not member accounts in a source Entra ID directory.
I am unable to find “Multitenant collaboration” in my tenant as an option to enable. Wondering if this feature hasn’t rolled out yet to some tenants ?
It’s definitely only available for tenants configured for targeted (early) release. Is that your state?
Hi Tony, do you know if the tenant as to be in “targeted release for everyone” or would “targeted release for select users” would do the trick ? I only have a few admin account in that state.
I don’t know. The simple test is to see if the option to establish an MTO is in your organization profile settings. If it is, you’re all set. If not, you’ll have to wait.
Targeted release for select users works as long as the admin doing the configuration is included in that targeted release group.
Very interesting question .. 🙂
Will MTOs replace the need for some tenant-to-tenant migrations or will an MTO be the opening step for others?
That is a very interesting question that we will have to parse out over the coming months…
Very interesting and helpfull.