Releases Cumulative Updates for Exchange 2016 and Exchange 2019 and Much More

On April 20, Microsoft announced the release of cumulative updates (CU) for Exchange Server 2016 and Exchange Server 2019. This is the first use of a new servicing model which moves from a three-month cadence for cumulative updates to six-monthly releases in the two halves of each year, which is why we have Exchange 2019 CU12 and Exchange 2016 CU23. The H2 update will appear later this year and will be for Exchange 2019 only as mainstream support is now over for Exchange 2016. The H1 CUs include the March 2022 security updates.
Microsoft says the new servicing model is in response to customer feedback that they simply couldn’t cope with testing and deployment of cumulative updates every three months. They’re going to target releases every March and September, but stress that quality rather than dates will govern when CUs appear. Many companies (including Microsoft) don’t like applying software updates at year-end, so Microsoft will avoid releasing a half-yearly CU in December. Microsoft also stresses that the extra gap between CUs means that they might release interim hotfixes should the need arise.
There’s evidence to suggest that the unrelenting update cycle is one reason why so many Exchange on-premises servers lag behind the desired state of having the latest or latest -1 update installed. Hopefully, the extra time between updates will relieve some pressure. At the very least, it removes an excuse for not applying updates in a timely manner.
The new release cycle is a good thing. Microsoft has known for a long time that some customers struggle with the three-monthly update cadence, so some of the pleasure in seeing this happen disappears when reflecting that the half-yearly cycle should have come a long time ago. Certainly, an arguable case exists that easier updates would have closed some of the gaps exploited in the Hafnium exploit last year. But that’s with the undoubted benefit of hindsight, and it’s always easier to be wise after an event.
The Great Last Exchange Server Issue
Companies with hybrid Exchange organizations don’t like being forced to keep an on-premises Exchange server after migrating all mailboxes to Exchange Online. The reason for the server is to manage mail-enabled recipient properties. It’s been a running sore for years and customers have roundly criticized Microsoft for apparent inactivity.
Now Exchange 2019 CU12 comes with an updated Exchange Management Tools role that can be installed on a server to allow recipient management through PowerShell. No other Exchange component is necessary. Microsoft says that “you can install the updated tools on a domain-joined workstation, shut down your last Exchange server.”
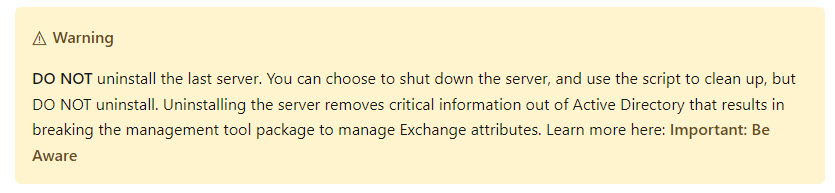
The important clarification here is that you can shut down but not run the Exchange setup program to uninstall the last server. If you do, you’ll remove the Exchange organization, and that would be a bad thing (if the on-premises organization doesn’t exist, the hybrid organization ceases). Instead, once you validate that the management tools work in your environment, you can turn off the last Exchange server and send it for recycling. The warning is clear in the documentation (Figure 1), but it might be overlooked.
As pointed out by Steve Goodman, it will take time to digest Microsoft’s documentation and figure out the strengths and weaknesses of the approach, but at least it’s a step in the right direction.
Hybrid Keys and More!
Many criticized Microsoft for not making free licenses available to allow companies to run Exchange 2019 on hybrid servers. Exchange 2019 CU12 closes the gap, and it’s very welcome.
Another important change is support in Exchange 2019 CU12 for deployment on Windows Server 2022. See the Exchange supportability matrix for more information.
Finally, the Microsoft Applications and On-premises servers bounty program now includes Exchange Server. In other words, Microsoft will make payments ranging from $500 to $30,000 to people who find and report vulnerabilities in Exchange Server. The same program includes the Teams desktop client and SharePoint Server. Let’s hope that security researchers can gain from the bounty program and help the community by squashing vulnerabilities before the bad guys exploit gaps in server defenses.




If you have Exchange 2016 with a full hybrid to 365 and all the mailboxes are migrated over can you install the Exchange 2019 Management Tools and and proceed to shutdown (not uninstall Exchange 2016? I can’t seem to find this answer anywhere.
I found your article very useful when it was first Posted, I am now wondering if you have made any further discoveries or recommendations including in relation to this recent post.
https://techcommunity.microsoft.com/blog/exchange/upgrading-your-organization-from-current-versions-to-exchange-server-se/4241305
Hi if you have Exchange 2013, can you install the 2019 cu12 Exchange Management Tool or would you have to upgrade to the 2019 full Exchange server before you would be allowed to add the tool?
Do you know off hand if a schema extension is required for exchange 2019 CU12?
No. See https://docs.microsoft.com/en-us/exchange/plan-and-deploy/active-directory/ad-schema-changes?view=exchserver-2019#exchange-2019-cu12-active-directory-schema-changes
Hi Tony,
Thanks for highlighting and clarifying that last Exchange should not be uninstalled!
The above it true for an Existing Hybird environment.
How about a greenfield scenario? i.e. you are setting up a new exchange environment with Exchange online and would want to manage the Exchange attributes using Exchange Hybrid.
Will this still require having an Exchange 2019 locally installed and then run the HCW or will the new release of Exchange 2019 CU12 (will this set up the Exchange Organization) should be enough followed by an HCW?
If you need to create a new Exchange on-premises organization, you can install an Exchange 2019 CU12 server, run HCW to establish the hybrid connection, and then remove the server to manage recipients afterward.
Thanks for sharing.
Hey Tony,
I don’t get it!
You said:
“Now Exchange 2019 CU12 comes with an updated Exchange Management Tools role that can be installed on a server to allow recipient management through PowerShell. No other Exchange component is necessary”
Is it already not works at this way?
It does work like that today, but the role can only be installed on a server where Exchange is present. The update allows the role to be installed on a workstation without the rest of Exchange Server.
Very interesting, Wish to see much more like this. Thanks for sharing your information!