It’s been a while since we covered any compliance-related news here on Practical 365, and the good folks at Microsoft haven’t been staying idle. Apart from the myriad of announcements we got at Ignite, many smaller improvements have been put on the roadmap or already released, so let’s run through them.
Sensitive Information Types updates
Making sure that the definitions of Sensitive Information Types (SITs) stay up to date is a never-ending battle, as evident from the frequent, and massive updates Microsoft has been making in the area (see the documentation changelog). Some of the changes revolve around “unbundling” the GDPR-specific types that were introduced a while back to cover scenarios for EU countries. Those SITs include:
EU Tax ID
EU National ID
EU SSN
EU Passport
EU Driving license
While using such SITs makes it easier to target EU-specific data, it also leads to some problems. Most importantly, it makes it impossible to tell which particular country’s data was detected, or similarly, to configure a rule that targets only Bulgarian passports, for example. And of course, as the definitions vary significantly across the individual countries, Microsoft had to use relatively weak patterns, which led to a considerable number of false positives.
To address these issues, a new set of country-specific SITs has been introduced, replacing the “generic” EU-based ones. At the time of writing this article, a set of 42 SITs that cover Tax ID and National ID across all member states of the EU has been GA’d. With 50 more SITs released in preview to cover the remaining scenarios (replacing the “bundled” EU SSN, EU Passport and EU Driving license SITs). As listing all these will take up a lot of space, refer to the official documentation for additional details. In addition, few other existing SITs have received definition updates, which you can again find in the aforementioned documentation article.
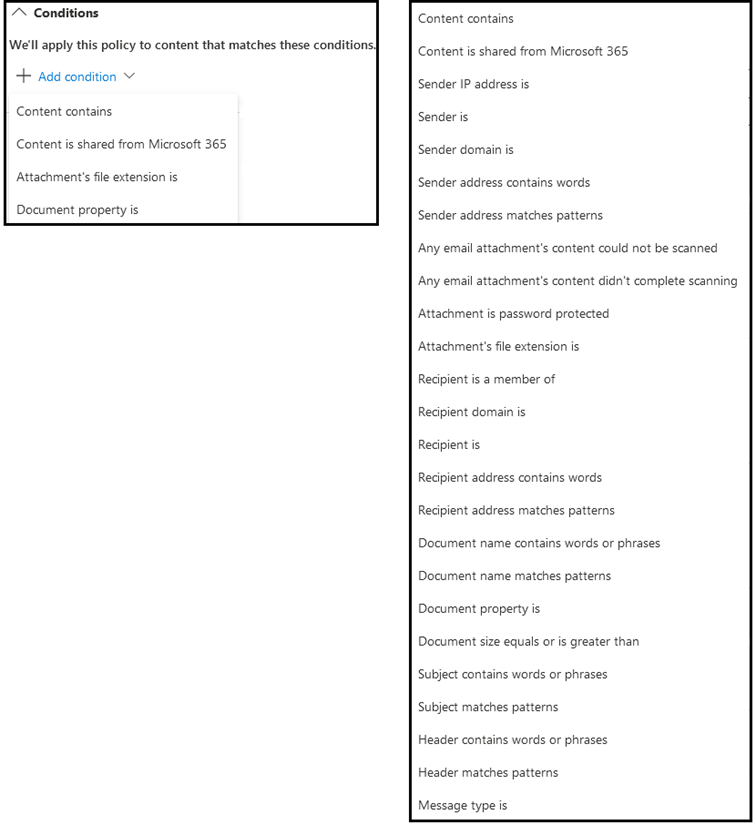
Parity of conditions and actions between Exchange DLP and Unified DLP
Unified DLP has been around for some time in Office 365. While it offered some obvious benefits, such as being able to cover multiple workloads with a single policy, the rules utilized by it lacked the granularity one might be used to when dealing with workload-specific DLP controls. This was most prominent in the case of Exchange Online, where thanks to the robustness of the Exchange transport rule pipeline, a large selection of conditions, exceptions and actions is available. With the move to Unified DLP, organizations weren’t able to utilize many of these conditions and controls.
Now, a few years after the initial release of Unified DLP, Microsoft is finally addressing this issue by introducing support for a multitude of new conditions and actions. An extensive list of newly supported conditions and actions is now in preview, with more to be added soon. Along with this, Microsoft has released a comprehensive PDF document to guide organizations in the process of migrating their old ETR-based policies to the new and improved Unified DLP engine. Later this year, a wizard-based UI will be available to facilitate the migration process, as well as the corresponding PowerShell cmdlet.
As the guidance spans 50 pages or so, we will obviously not be able to cover all aspects here, but we can make some basic comparison. On the screenshot below, you can see the list of conditions supported by Unified DLP until recently on the left, whereas on the right you can see the updated list:
and the same applied to Actions:
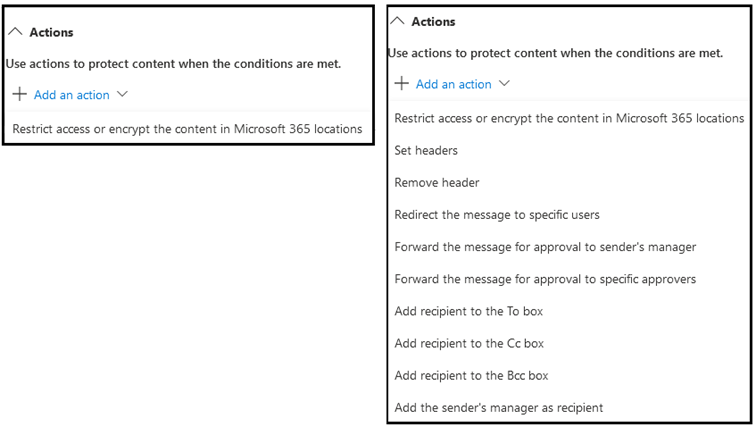
The first thing to mention here is that the vast majority of these conditions/actions will only be available for Unified DLP policies where Exchange Online is selected as the only location. If multiple locations are selected, the list will be trimmed to reflect the selection, and only conditions/actions supported by all locations will be displayed. As a side note, the UI in the good old SCC seems to list all conditions regardless of the selection made for locations, but at this point, you should be using the new and shiny Microsoft 365 Compliance Center anyway.
The list of supported conditions, exceptions and actions is too long for us to cover each of them, so instead, we can focus on what’s missing and a few caveats. A few conditions are still unavailable, such as those comparing properties of both the sender and recipient (the sender’s relation to recipient is, the message is between members of these groups, the manager of the sender or recipient is this person, and the sender and recipient property compares as). For other conditions, a direct replacement might not be available, but a workaround is. These include:
- has specific properties including any on these words, and has specific properties matching these text patterns conditions for both sender/recipient, with the suggested replacement being using a group along with the member of condition;
- a set of contains any of these words or matches these text patterns conditions to be replaced with the content contains condition; applies to text in subject and/or body and/or any attachments;
- the message contains any of these types of sensitive information to be replaced with the content contains condition;
- the message properties include this classification to be replaced with content contains > sensitivity label condition;
- any attachment has these properties, including any of these words to be replaced with the document property condition;
For a full list, refer to the PDF document linked above. Also, note that some of the conditions listed as available might still be in preview, but will be available once the feature reaches GA status. Same applies for actions, which we will discuss next.
As with the conditions list, some actions have been replaced by equivalent functionality. These include:
- Redirect the message to hosted quarantine, the suggested replacement being a forward message for approval action;
- the set of Block the message… actions to be replaced with the Restrict access or encrypt the content in Microsoft 365 locations functionality or Endpoint DLP controls;
- Modify the message properties > apply a message classification and Modify the message security > apply Office 365 Message encryption and rights protection actions to be replaced with the Restrict access on encrypt the content… > Encrypt email message > Select label functionality (not available at the time of writing);
Some actions such as Redirect the message to the following connector, Require TLS encryption, Set spam confidence level and Apply custom branding to OME messages will not be available. Others, such as Apply HTML Disclaimer, Prepend subject or Remove OME are work in progress and will be available soon. Actions such as User notifications, Policy tips and Incident reports have their own corresponding controls within a Unified DLP policy and have been available for a while.
To summarize, Microsoft has made a great step forward and brought many of the conditions and actions we are used to from robust Exchange transport rules/DLP to Unified DLP. They’ve also made sure that the process of migrating your existing ETR-based DLP policies will be as smooth as possible by releasing detailed guidance, with a wizard-driven workflow to follow in the coming weeks/months. Lastly, Microsoft is working on ensuring that we can continue using an “encrypt” action, now in a “unified” way thanks to the integration with the MIP suite. To top it all, Microsoft has also GA’d the Endpoint DLP solution, extending the reach of Unified DLP to Windows 10 devices. But this is a topic for another article…
Some additional updates
To close of the article, lets cover some other compliance-related news. First, the Records management role group will be updated to include additional roles, allowing users assigned said role group to access all functionalities of the Records Management solution. The actions include: managing retention labels, publishing and auto-application of labels, managing retention events, manage disposition. The changes should be hitting a tenant near you before the end of the year.
The Data investigation functionality, which launched in Preview in August 2019, is set to be retired by the end of the year. Organizations have until December 31st, 2020 to review each Data Investigation case and replace it with matching functionality in Core or Advanced eDiscovery. As to why Microsoft decided to discontinue this new feature, no clear reasons are given, but this is hardly the first functionality within the Office 365 suite to be sunset.
Some more cryptic updates have also made it to the Message center recently. Those include the public preview of Microsoft 365 Audit retention dashboard, which will supposedly replace the current experience of managing audit log retention policies, and a new service plan, Data classification in Microsoft 365, which is supposed to “support improving the performance of our sensitive information“?! No information is currently provided as to how exactly a service plan will improve performance and on what, how it relates to the Data classification solution, which SKUs it will be a part of, which users will it need to be assigned to, if any, and so on.
Lastly, a new Data-at-rest encryption service is launching in preview, to replace and extend the existing Customer Key feature set. We will cover this in a future article.


