Sensitivity Label Settings to Reveal Private Teams Appear to Users
Message center notification MC683664 (23 October 2023) promised a new approach to managing the discoverability of private teams. Discoverability means that teams are candidates to appear in the set of suggested teams displayed when people use the Join a team feature. Public teams appear in the list but private teams do not, which means that users have no idea about the private teams that exist in an organization.
Previously, the Set-Team cmdlet allowed administrators to mark a private team as “discoverable” by setting the ShowInTeamsSearchAndSuggestions parameter to True. Microsoft removed this capability, much to the chagrin of tenant administrators. As this contribution attests, the result could be an increase in team sprawl when people created teams because they didn’t know about existing teams.
Microsoft originally planned to roll out their new solution to targeted release tenants in mid-October 2023 followed by general deployment in January 2024. Those dates have slipped and Microsoft now plans to make the update available at the end of January 2024. As always, it will take time for the new code to land in all tenants.
Updating Teams Policies to Control the Discoverability of Private Teams
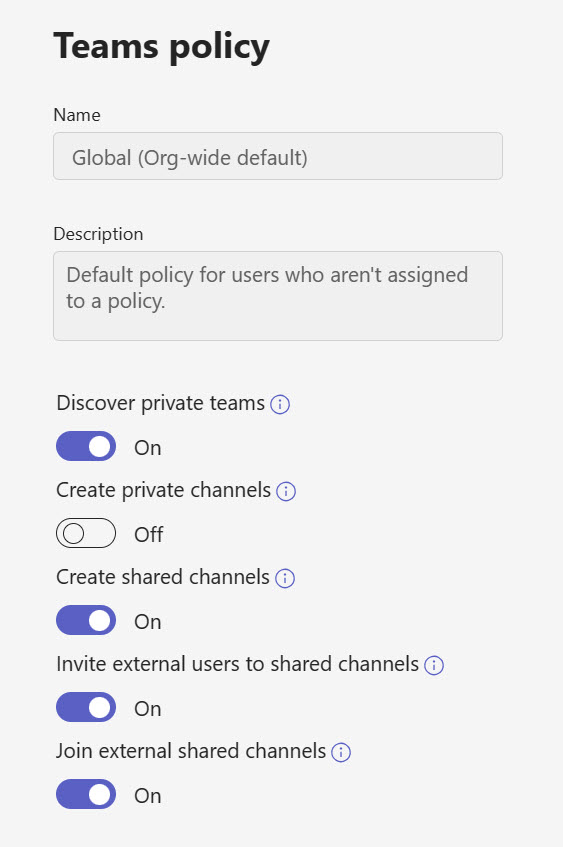
The new plan introduces a setting in Teams policies to control the discoverability of private teams for users covered by a policy. This is a broad-brush approach that’s suitable for organizations that want to make private teams discoverable for large numbers of users. Figure 1 shows the setting to make private teams discoverable in a Teams policy.
Making private teams discoverable does not remove the requirement for users to request permission to join a team. Once they find a team that they’d like to join, users must send a join request for a team owner to approve (or not).
By default, Teams policies block the discoverability of private teams. If this doesn’t suit your tenant (perhaps because you want to use a more granular approach), you can enable the setting through the Teams admin center or with PowerShell. Unfortunately, the Set-CsTeamsChannelPolicy cmdlet does not accept pipeline input, so each policy must be enabled separately. Here’s the command to enable the discoverability of private teams for accounts assigned the default Teams policy:
Set-CsTeamsChannelsPolicy -EnablePrivateTeamDiscovery $true -Identity Global
Using Container Management Sensitivity Labels to Control the Discoverability of Private Teams
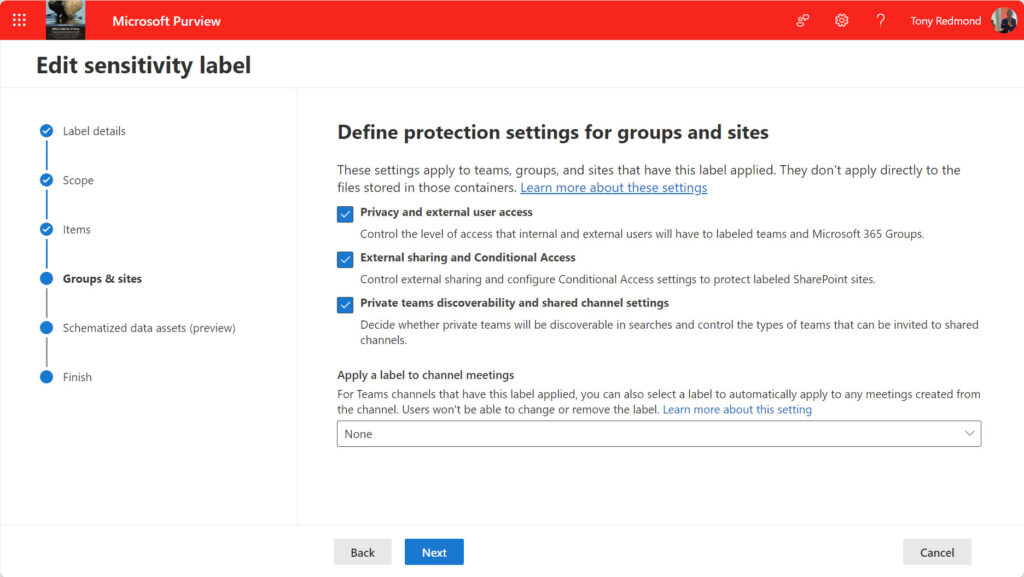
A more granular control is also available in the form of a new container management setting for sensitivity labels. A sensitivity label intended for container management holds settings to control elements like guest user access and visibility. When a container (like a team) is assigned a label with container management settings, it inherits those settings. Team owners cannot update the setting inherited from a label. Essentially, private teams assigned a sensitivity label with the setting turned on are discoverable while those assigned labels with the setting disabled are not. The discoverability control set by a sensitivity label takes precedence over the Teams policy for a user account.
My tenant has several container management labels defined to apply settings to groups, teams, and sites that receive the labels. For example, teams that support confidential discussions receive the Confidential Access label. The settings of this label include the necessary settings to prevent the teams assigned the label from being discoverable. The other container management labels allow discoverability.
To configure the Confidential Access label, I edited its settings and checked the box to control Teams discoverability settings (Figure 2).
I then moved forward to the page where Teams discoverability settings are defined and made sure that the checkbox to allow users to discover private teams is unchecked (Figure 3).
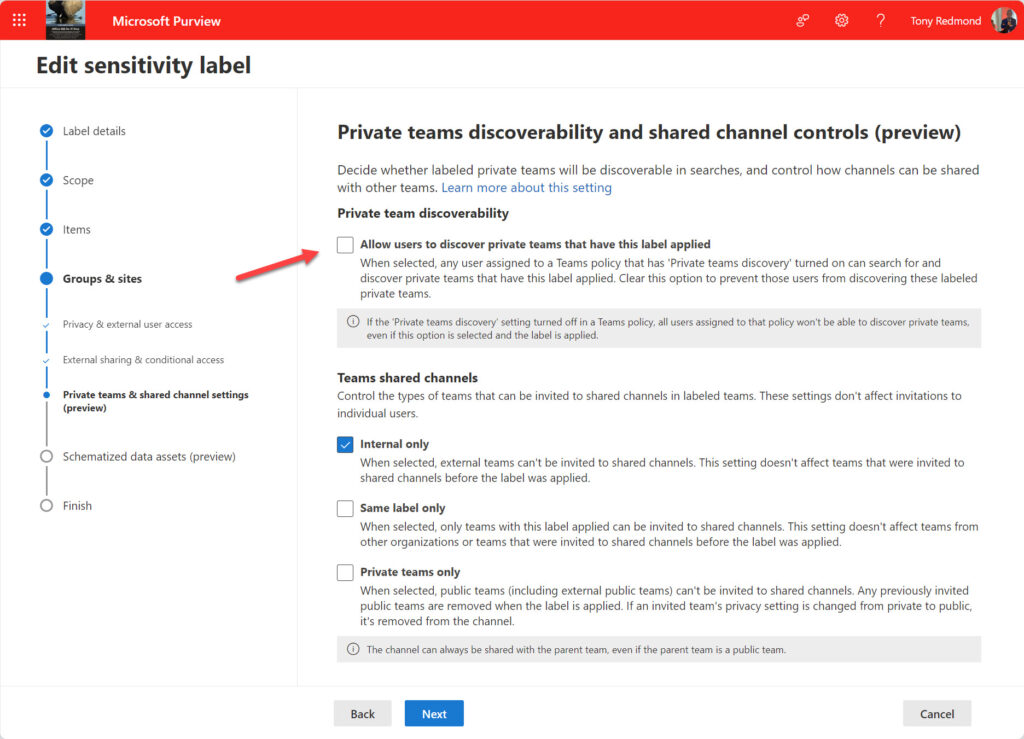
The net result is that any team assigned the Confidential Access label is not discoverable. I don’t like the way that the two settings are involved on different pages as it would be simpler to have a single on/off setting to control discoverability. It’s easy to check the box on the first page and forget to check the box on the second and end up with undiscoverable teams.
Using the techniques explained in this article to use PowerShell to report label settings, we can see that the setting used to control private teams discoverability is called allowprivateteamstobediscoverableusingsearch.
Label : Confidential Access Applies : Site, UnifiedGroup Priority : 29 Section : protectteamschannel Subtype : Key : allowprivateteamstobediscoverableusingsearch Value : false
The discoverability setting is a simple true/false switch, so it seems like Microsoft has overcomplicated the label setup, unless of course, they plan to add more label settings to control other aspects of team behavior.
Proving the Point
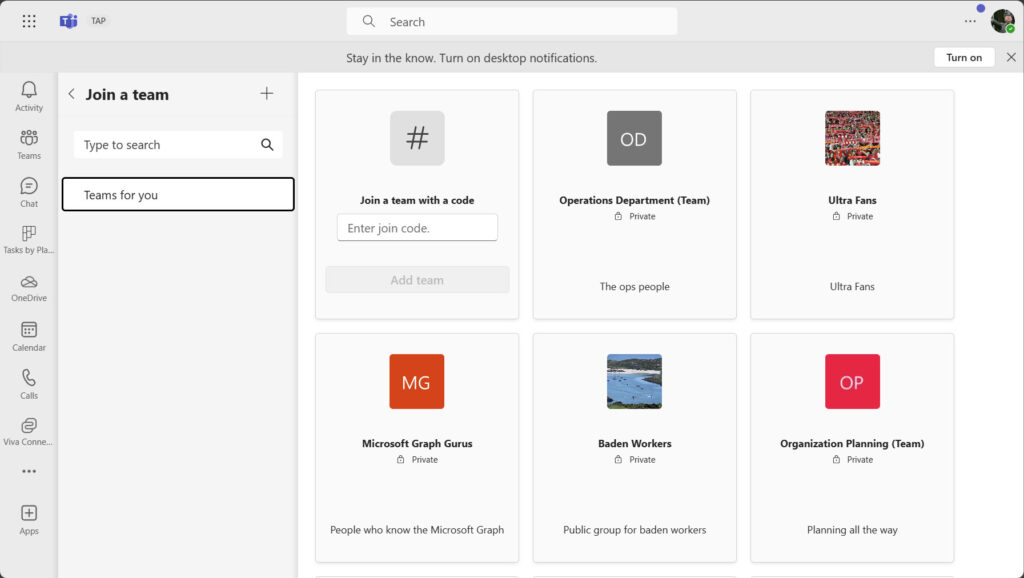
With everything in place, it’s time to test if the feature works. Figure 4 shows the Join a team gallery displayed to a user. A mixture of public and private teams are present because the Teams policy assigned to the account allows private teams to be shown. However, none of the private teams has the Confidential Access label because the label settings block discoverability.
To be sure that the join a team gallery exposes teams that are discoverable, we use the Get-Label cmdlet to check the identifier for the Confidential Access label:
Get-Label -Identity 'Confidential access' | Format-Table DisplayName, ImmutableId DisplayName ImmutableId ----------- ----------- Confidential Access c99e52c6-f5ff-4050-9313-ca6a3a35710f
And then use the Get-UnifiedGroup cmdlet to check the identifier of the labels assigned to the private groups in the gallery. For instance:
'Ultra Fans', 'Baden Workers', 'Organization Planning (team)', 'Microsoft Graph Gurus', 'Operations Department (Team)' | Get-UnifiedGroup | Format-Table DisplayName, SensitivityLabel DisplayName SensitivityLabel ----------- ---------------- Ultra Fans e42fd42e-7240-4df0-9d8f-d14658bcf7ce Baden Workers e42fd42e-7240-4df0-9d8f-d14658bcf7ce Organization Planning (Team) e42fd42e-7240-4df0-9d8f-d14658bcf7ce Microsoft Graph Gurus e42fd42e-7240-4df0-9d8f-d14658bcf7ce Operations Department (Team) e42fd42e-7240-4df0-9d8f-d14658bcf7ce
All of the private teams presented to the user are discoverable because they don’t have the Confidential Access label.
Managing Shared Channels for Private Teams
The setting to control the discoverability of private teams appeared first. Subsequently, Microsoft issued MC709659 (January 24, 2024) to say sensitivity labels can control the types of teams that can be invited to participate in shared channels belonging to labeled teams. The options are visible in Figure 3 and are:
- Internal teams only: Only teams from the same tenant can be invited.
- Same label only: Only teams assigned the same sensitivity label can be invited.
- Private teams only: Only teams with private membership can be invited. When the label is assigned to a team, Teams checks shared channels for public teams and removes any that are found. If a team owner subsequently changes the privacy for a team in the shared channel from private to public, Teams removes the team from the shared channel.
If the setting is internal teams only or same label only, it controls what teams can join shared channels in the future. It has no retrospective effect on affect teams that currently participate in shared channels belonging to labeled teams.
A New Start to Discoverability
Microsoft’s new method to control private team discoverability looks solid and delivers both broad-brush and granular controls. My only quibble is the setup for the container management labels, but this is a once-off operation that shouldn’t kill too many brain cells, so it’s probably OK.





I have enabled the Discover Private Teams feature for our global Teams policy, but it doesn’t seem to have done anything. Any advice? (GCC Tenant).