Do you have more than five Global or Service Admins in your tenant? Do you know what changes are being made in your tenant daily across your services? Having too many Admins can create chaos between departments if communication is lacking. As an Office 365 Global Administrator, shouldn’t you know what changes are being made? Searching audit logs is not an ideal way of spending your time, not when you can automate alerts in Office 365 instead.
Enter Activity Alerts. Creating Activity Alerts is a great way to inform you of changes made throughout your tenant. They can alert you to services or users in your tenant based on some criteria of attributes in the audit log. You can view the full list here.
Global Administrator accounts can get compromised. If you do not have auditing enabled then it will be hard to figure out what, if anything, changed in your tenant. Here’s an article showing breached Global Admin accounts for sale on the dark web.
How to set up Activity Alerts
First, you’ll need to turn on Auditing and then create a test Activity Alert.
Ensure Auditing is in enabled in your tenant.
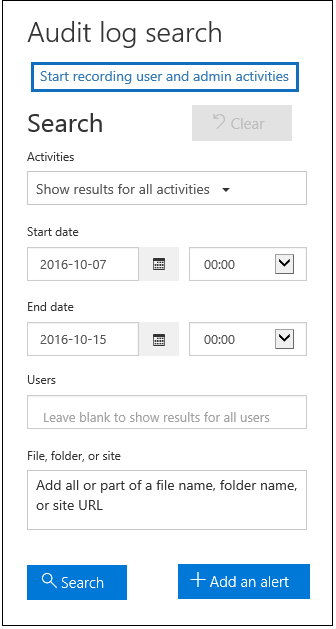
Login to the admin portal and go to Security & Compliance. Go to Search & Investigation then Audit Log Search.
If Auditing is not enabled for your tenant yet let’s enable it now. Click on Start Recording user and admin activities. A dialog box will appear. Click Turn On. A message will display saying the audit log is being prepared and you can run a search in a few hours.
If you would like to enable via PowerShell you can do so with the following command.
Connect to Exchange Online Protection and the Security & Compliance Center PowerShell Module. Execute the following:
Set-AdminAuditLogConfig -UnifiedAuditLogIngestionEnabled $true
Creating Activity Alerts
We will walk through an example of Global Admins creating Transport rules. This is very useful if Global Admins across the globe are making changes that you are not aware of. A compromised Admin Account could create a new transport rule without your knowledge. They could then send your email to external email addresses. Transport rules aren’t something you’re creating and modifying every day. Yet they could be worth alerting on if you have a large complex environment with hundreds of rules in place.
Commands
For a list of Activity Alert parameter sets, you can review the following article here. Take note in the article of the section for “-recordtype”. This will help you in labeling the alerts. Also, if you do not specify a “-userid” parameter, the alert will apply to all users in your tenant.
The basics of what we need are the following:
New-ActivityAlert
– Name (the name of your alert)
– Operation (the command executed)
– Notifyuser (email address to send the alert)
– UserId (whom the alert is being triggered against, ie. Global admin accounts in our example)
– Description (obvious here)
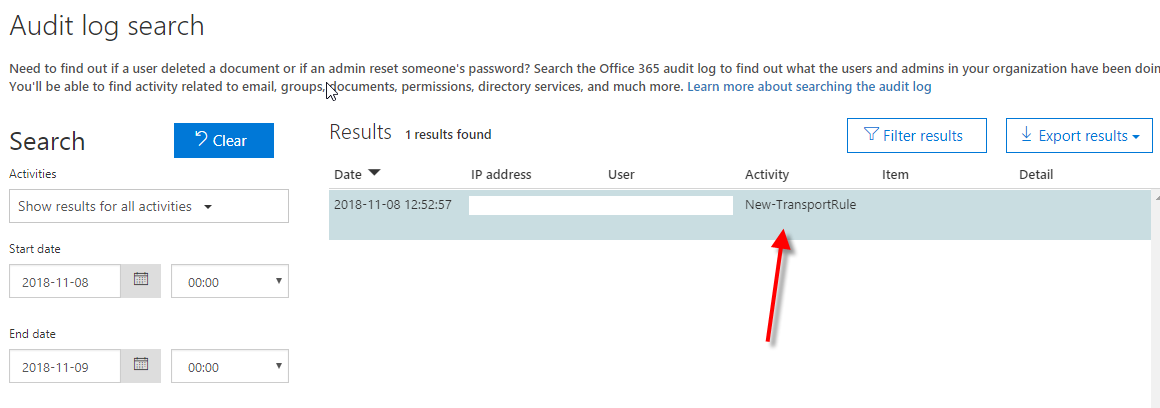
In the example below, we will be testing with Transport rules. I’d like for you to create a basic transport rule in your Exchange Admin Portal for testing purposes. If you are not familiar with creating a transport rule you can learn about it here. After the transport rule is in place, you can go back to Security & Compliance Center. Then go to Search & Investigation and Audit Log Search. In the Users section put in the name of your admin account, adjust the date to today and then click Search.
Results will show under the Activity section. The “New-TransportRule” entry in the audit log.
Any executable command in Office 365 logged in the audit log can have an Activity Alert created. This is a great way to create new Activity Alerts of changes to settings in your tenant.
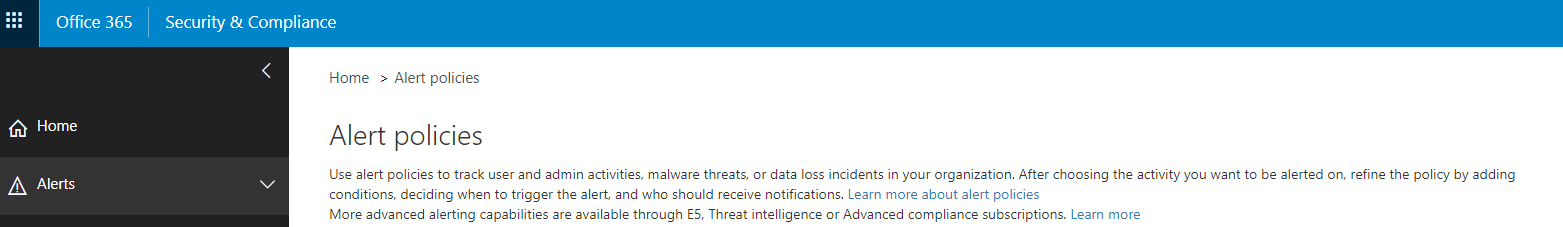
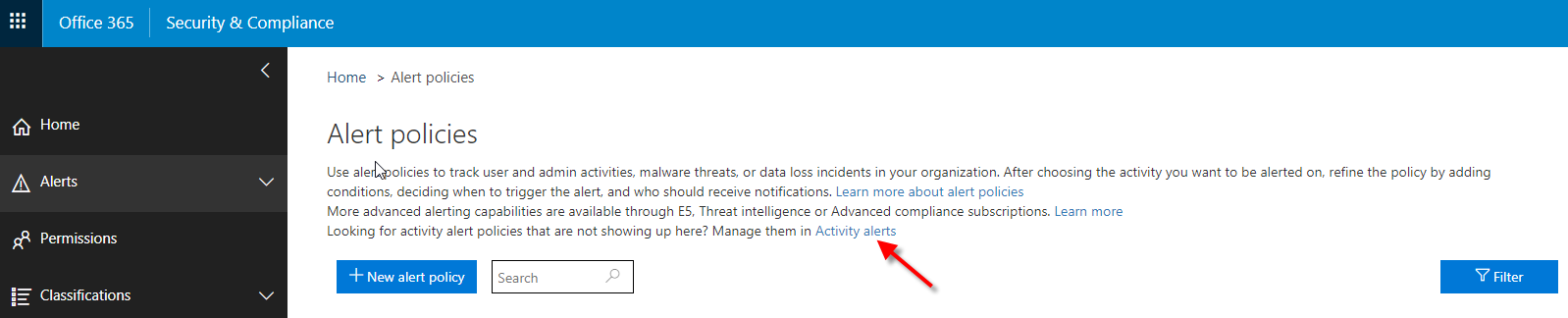
Activity Alert Management via the portal
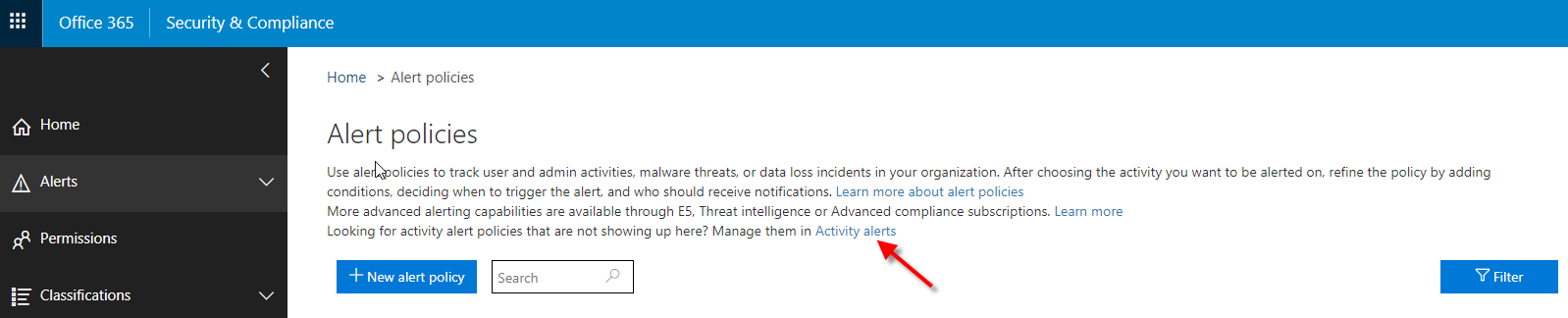
Login to Office 365 admin portal and browse to Security & Compliance Center. Expand Alerts and select Alert Policies. Manage Activity Alerts section is not listed at first. To get to the management portal you will need to create an Activity Alert first via PowerShell. Once you create an Activity Alert will you then be able to see the management area in the portal.
Once you create an Activity Alert will you then be able to see the management area in the portal.
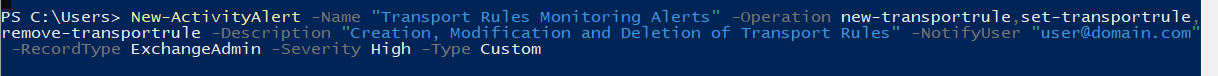
Creating a Transport Rule Activity Alert
Let’s create a new alert for any time someone creates, modifies or removes a transport rule.
Login to Exchange Online Protection and Security & Compliance Center PowerShell Module. Run the following. Update settings as needed.
New-ActivityAlert -Name "Transport Rules Monitoring Alerts" -Operation new-transportrule,set-transportrule,remove-transportrule -Description "Creation, Modification and Deletion of Transport Rules" -NotifyUser "user@domain.com" -RecordType ExchangeAdmin -Severity High -Type Custom
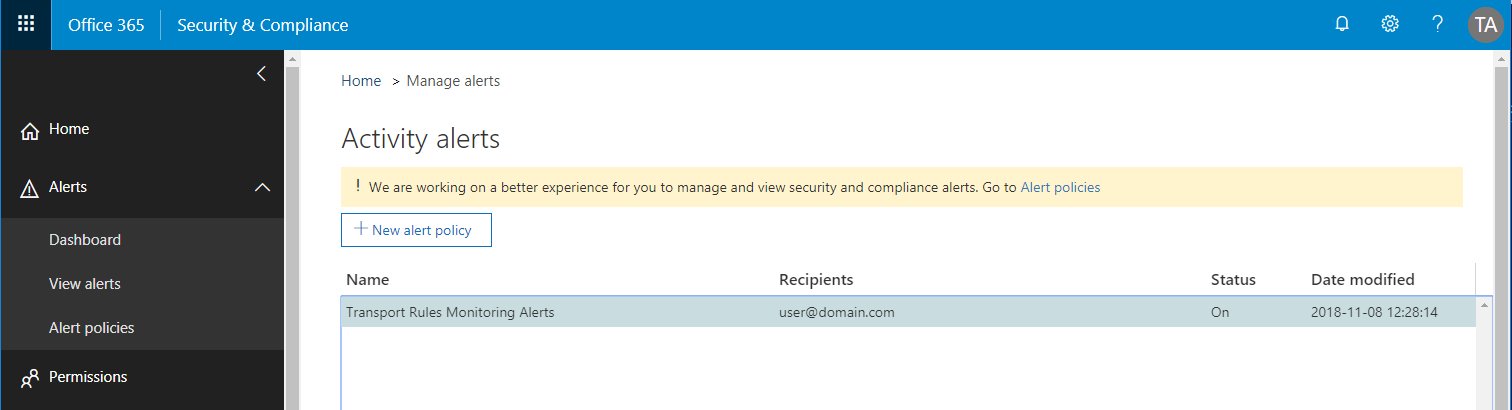
Now that this is complete, go back to the Alerts Policies. Click the Activity Alerts at the top of the screen.
This will take you to the Activity Alerts management page.
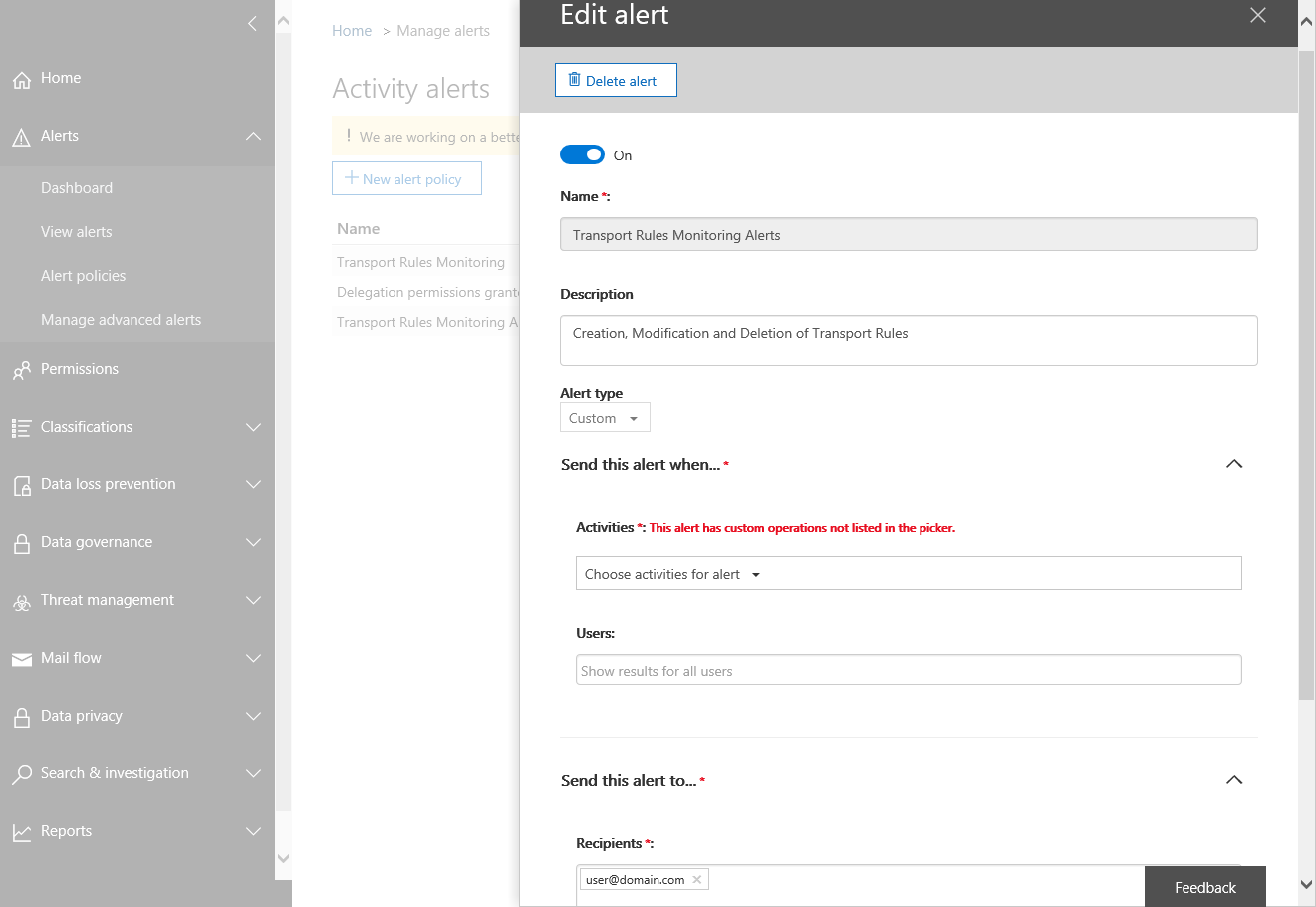
When looking at the alert in the portal you will see you cannot view the activities since this is a custom rule set. Execute the get-activityalert command in your PowerShell session. This will show the actual properties of the custom rule. You can find the details here on get-activityalert commands.
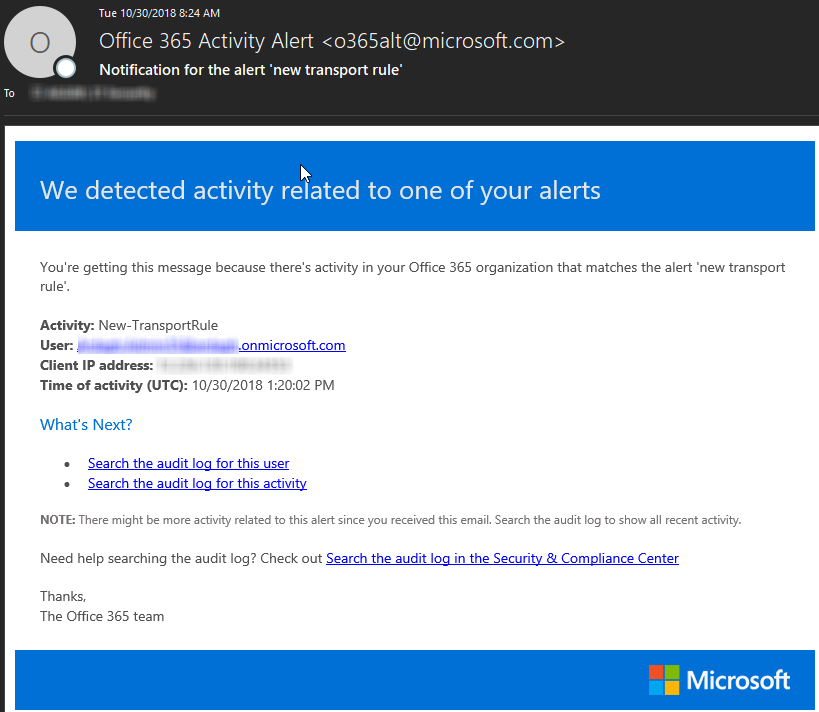
Now that the Activity Alert is in place, go ahead and create another test transport rule. You will receive an email notification about the new rule that you created. The email notification will look like below.
Alert settings via the portal
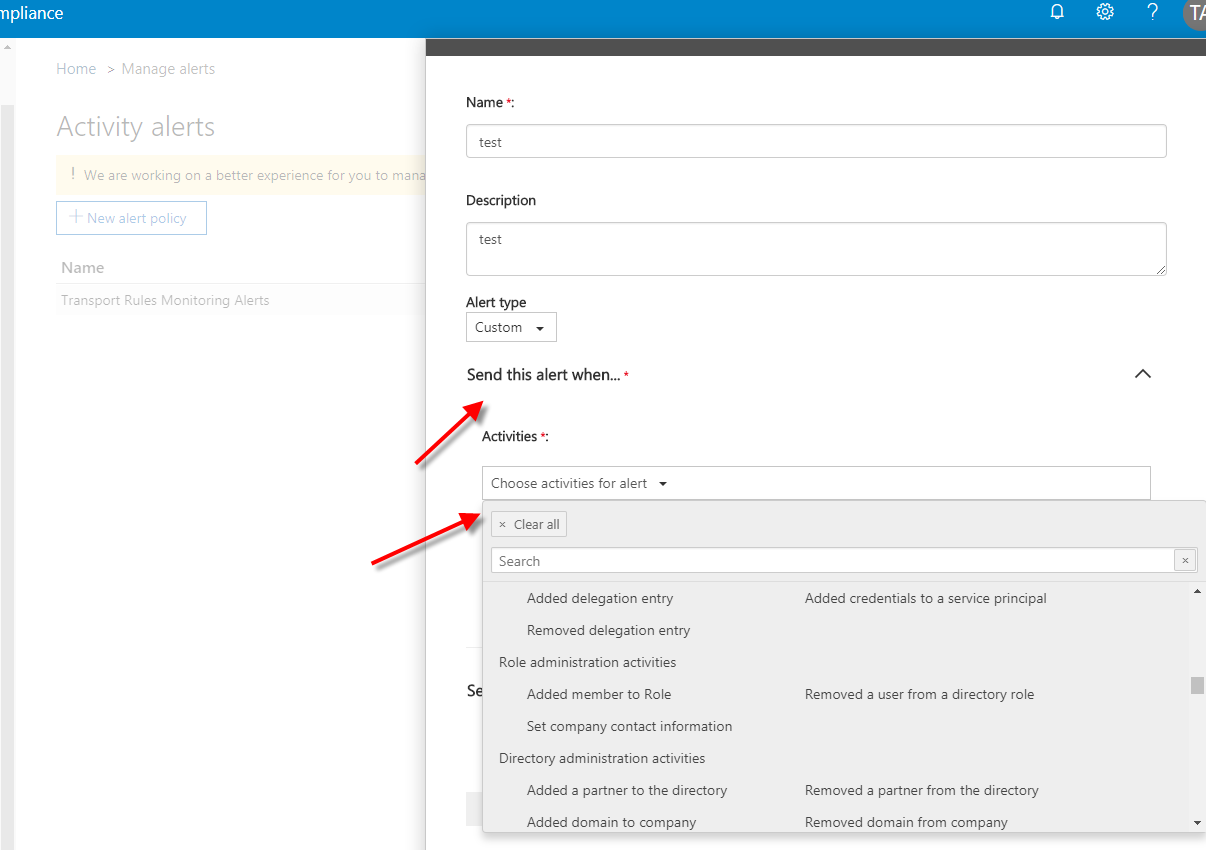
There are hundreds of alerts already available to get you started. Let’s go back to the Activity Alert page and select New Alert Policy. Select the drop-down for Send this alert when. In Activities, you can select the drop-down for Choose activities for alert. Look at the many items you can create Activity Alerts on. For a full detailed list of all items available here. You can read the full details under the Audited Activities section.
Summary
As you can see, the number of Activity Alerts for each Office 365 platform are a great start. There are many options not listed here. You will need to investigate the audit logs to get the executed commands. Once in hand, creating Activity Alerts will keep you aware of changes in your tenant. Whether planned or malicious.
Microsoft’s Office 365 Secure Score recommends no more than five Global Admins. If your tenant must have more than five Global Admin accounts, make sure you know exactly who and what has changed in your tenant. Get to know Activity Alerts and put in place your own rule sets to stay on top of changes in your tenant. Work with your SharePoint admin and show them the possibilities available with Activity Alerts. Make their jobs easier with reporting on items they may not be aware of.
I hope this has a been a great learning experience for you. If you have any questions or would like to discuss, please comment below. Thanks!



Pingback: Tenant Alert Login - Official Site
nice article. Thank you!
Can we apply this activity alert to security group, DL or mail-enabled security group if want to apply for set of users in group?
I created the alert for all cases of Search and export e-mails/Psts, however, the item available for alert is e-Discovery.
When accessing the item Search and use of Content Search and export PST does not receive any alerts.
Hi,
Any ideas on how to setup an alert for Office 365 group creation? I’ve setup an alert on the activity “created group” however i want to exclude OneDrive locations
Looking forward to hearing from you,
hi , i followed all the above steps does’nt seem to trigger the email
as per technet it says
-Operation
The Operation parameter specifies the activity that triggers an activity alert.
A valid value for this parameter is an activity that’s available in the Office 365 audit log. For a description of these activities, see Audited activities.
Although this parameter is technically capable of accepting multiple values separated by commas, multiple values don’t work.
so should we add only one value ?
What is the best rule to create to monitor anytime tries to access email outside of the USA? I want to set an alert to monitor anytime anyone from an outside the USA tries to access outlook and send an email to the appropriate people.
You absolutely can. In the Activity Alert Panel, you can create new and for Alert type set custom. In Activity search for “added delegate mailbox permissions”. In the users box select the user you wish to monitor. Finally, configure an email address to send the alert to.
Can i create alert for one specific user? For example if any admin assign delegate access on a mailbox I want to see an alert.
Hi Tony. Im attempting to add a New Alert Policy from the Security and Compliance – Audit log search dashboard. I can create it however the alert does not appear in the Alerts dashboard. I can create a New Alert Policy from the Alerts – Alert policies dashboard and those appear. I need the coice of activities to audit that appear when creating from the S/I dashboard.