Sensitivity labels in Microsoft 365 have been around for quite some time. Essentially they enable users to apply protection to emails and documents that they’re working on by assigning a label to that content.
The purpose of this ensures that only people authorized to view or consume that content do so. You can configure sensitivity labels to apply encryption and content marking to specific emails and documents, which you assign to users or groups with varying permissions levels using labeling policies.
Depending on the level of Microsoft 365 licensing in place, these labels can be either manually applied by the end-users themselves, or automatically based on built-in sensitive information types. You can read more about the licensing requirements for Microsoft Information protection here.
Upcoming Webinar: How to Prepare for Office 365 License Renewal – September 21 – 10:30 AM ET / 15:30 PM BST / 16:30 PM CEST. Hosted by Microsoft MVP Paul Robichaux.
The evolution of sensitivity labeling can be traced back to Information Rights Management within Office 365, then Azure Information Protection in the Azure portal, and finally, Unified labeling via the Microsoft 365 Security and Compliance Center.
Up until recently, however, it was only possible to apply sensitivity labels to emails or documents. Microsoft has now introduced the ability to use sensitivity labeling at a ‘container level’, which means that you can apply for labels’ protection at a higher level than the document or email. In Microsoft 365, when we refer to containers, this currently relates to the following three features or services.
- SharePoint Online Sites
- Microsoft Teams
- Microsoft 365 Groups
This blog series will show you how sensitivity labeling works at the container level and configure existing labels. We’ll also show how this relates to any existing labeling applied at the document level and some useful tips on the M365 audit logs’ auditing capabilities.
We will start in the M365 Compliance Center, enabling some existing labels for use with containers.
Microsoft 365 Compliance Center
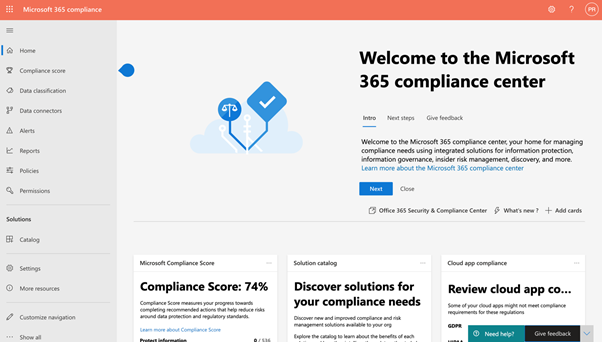
Over the past couple of years, the Microsoft 365 Security and Compliance Center has been my go-to portal for information governance and protection. Whist this portal remains available, the evolution of so many features relating to both Security and Compliance has led Microsoft to provide specific outlets to administer these functions. Therefore, we now have the separate Security Center and Compliance Center.
To demonstrate Sensitivity labeling at the container level, I will be working from the Compliance Center by completing the following steps.
- Log on to the Compliance Center as a Global Administrator, Compliance Data Administrator, Compliance Administrator or a Security Administrator. This will take you to the portal as shown below.
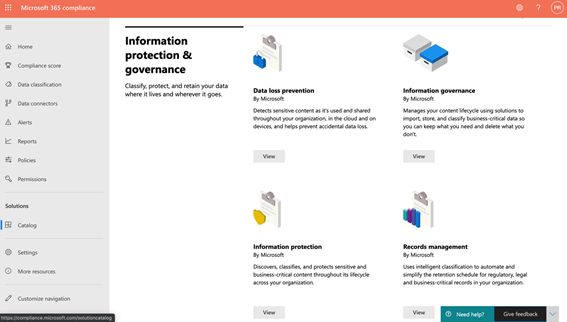
2. Next, click on Solutions > Catalog > Information protection > View.
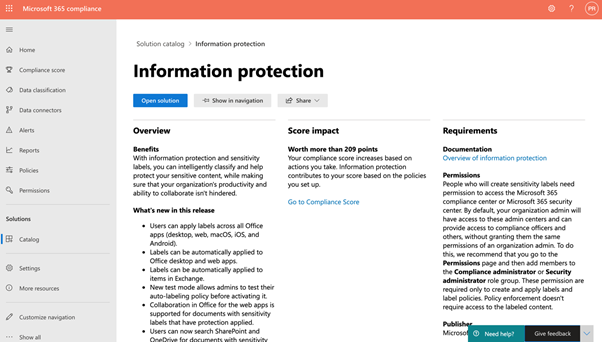
3. Now click on Open solution.
4. In the example below, we can see many of the labels and sub-labels already available in my tenant, currently providing encryption and content marking to emails and documents.
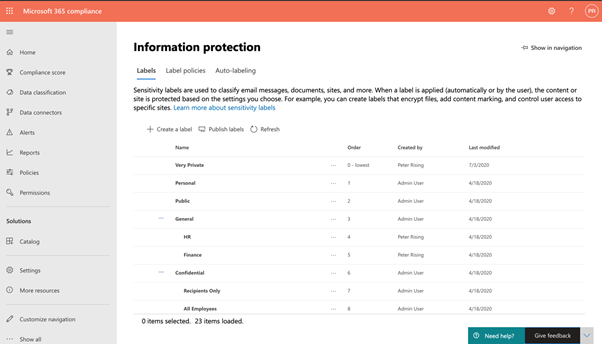
5. If we select the General / HR sub-label, we can note its existing settings as below.
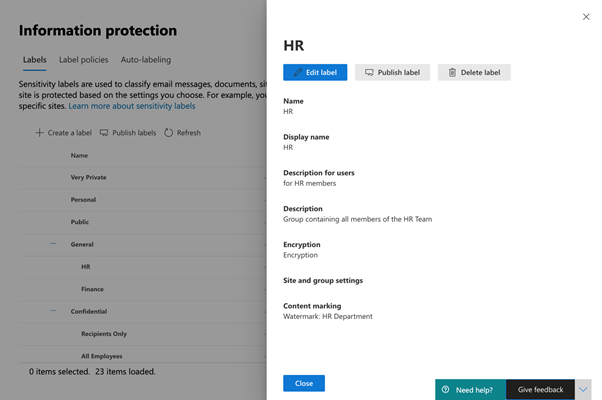
6. If you are already familiar with Sensitivity labels, you will note a newer section in this dialog called Site and group settings. Click on Edit label, and this will open the label wizard in the following image.
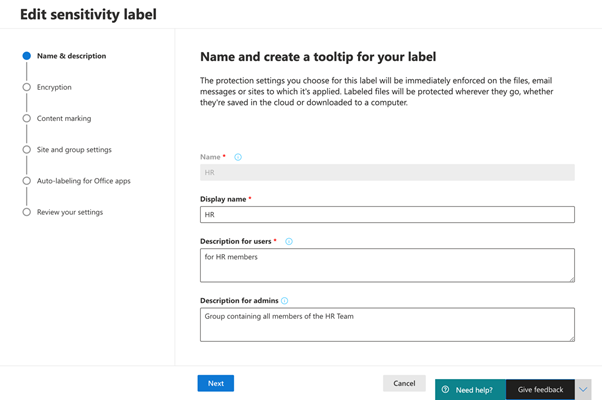
7. Keep clicking Next until you reach the Site and Group settings.
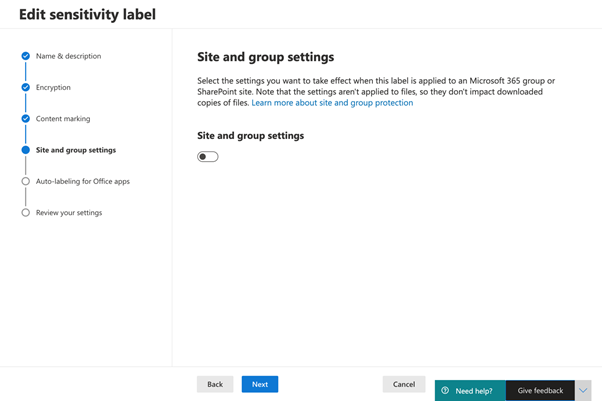
8. Move the slider to the on position, and this will present you with the options to configure the Site and Group settings.
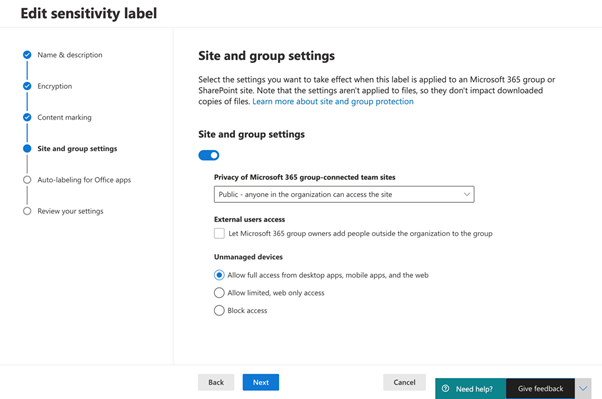
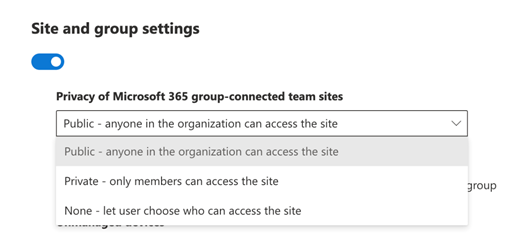
9. You can choose some privacy options from the dropdown menu to access the Site or Group where this label will be applied. These options are shown in the following table.
| Public | This will allow anyone in the organization to access the Site or Group where this label is applied. |
| Private | This setting restricts access to only approved members in your organization |
| None | This setting will allow the user to decide who can access the Site when the label is applied. |
10. In this example, we will set this label to be applied privately, meaning that only members will access the Site.
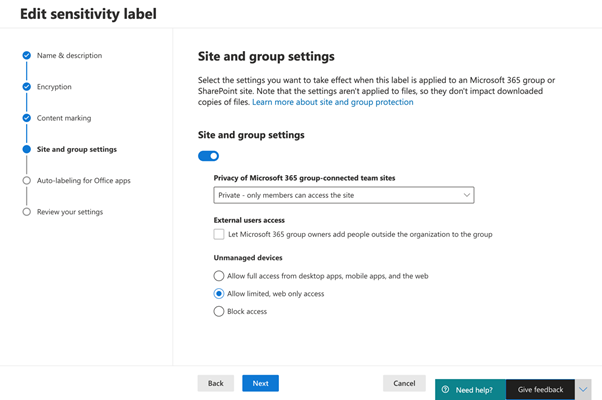
11. We can also choose whether we want Sites and Groups protected by this label to be accessed by people outside of the organization. In this example, we will leave this option unchecked.
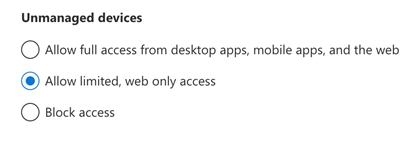
12. Finally, we have some controls to address which allow us to choose how any unmanaged devices when they attempt to access Sites or Groups protected by this label.
Note: To use this option, you will also need to configure the SharePoint feature, which uses Azure AD Conditional Access to block or limit access to SharePoint Online and OneDrive content from unmanaged devices. Further guidance on how you can configure this feature may be found here.
13. Now that you have configured the Site and group settings for your label, click through the wizard, and on the Review your settings page, click Save label.
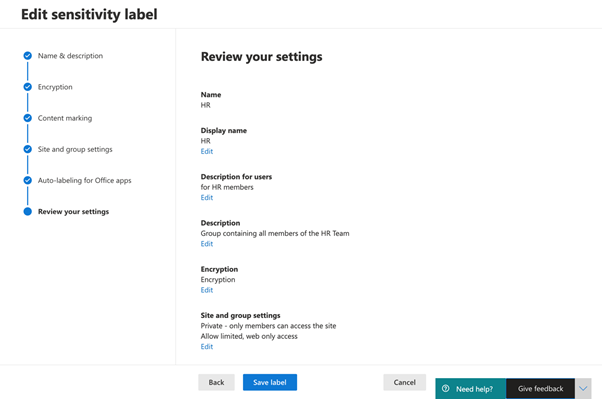
So, that’s how you can set up an existing label to be Site and Group ready. Now, let’s take a look at how this works in the first of our three M365 containers, which are SharePoint sites.
Applying sensitivity labels to SharePoint sites
Now that we have a configured label for use with sites and groups, we can apply that label to an existing SharePoint site within our M365 tenant, or whilst creating a new site. In the following example, I will choose to create a new Team Site to demonstrate how this can be done.
We need to complete the following steps.
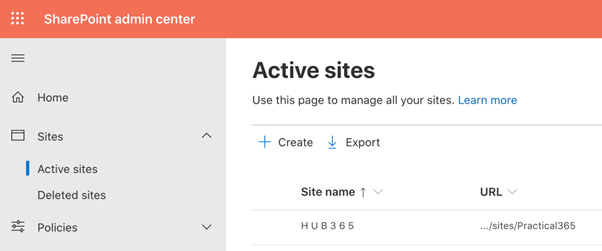
- Logon to the SharePoint Admin Center and navigate to Sites > Active Sites. Please refer to my previous blog series How to create Modern SharePoint Online Team Sites for instructions on how to connect to the SharePoint Admin Center. Click on Create.
2. Click on Team site.
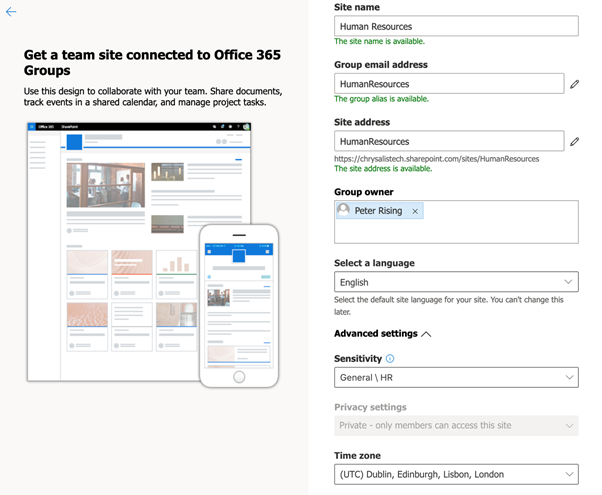
3. Enter the details to create your Team Site as shown below. In this example, we will create a site called Human Resources. Under the Sensitivity setting, we will select the General \ HR label, which we created earlier. Note that this selection results in the Privacy settings field is greyed out. This is because we set the chosen label as Private – only members can see this Site. Therefore, the privacy method is automatically applied.
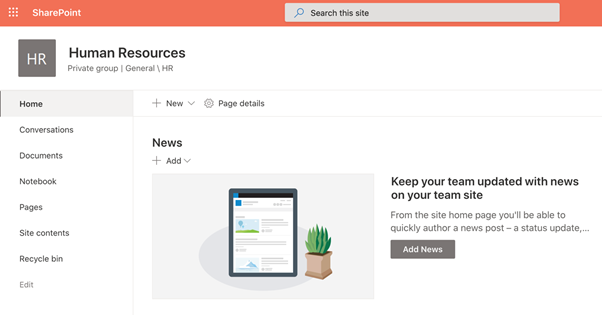
4. Complete through the wizard to finish creating the Team site, and then open the Team site by searching for it in the SharePoint Admin Center. As you can see below, we now have our new Team site ready, and it is appropriately labeled under the Site name as Private group | General \ HR.
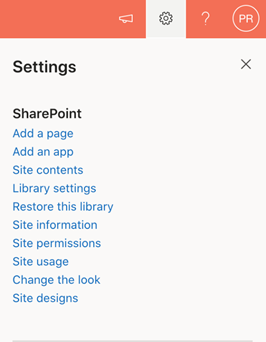
5. This label setting’s effect is that the Site is accessible only to members of the Site, and the Site cannot be shared externally as per the label settings. To demonstrate this, I will try and add an external email address as a member of the Site. I do this by clicking on the cogwheel and selecting Site permissions.
6. Next, I click on Invite people > Add members to Group.
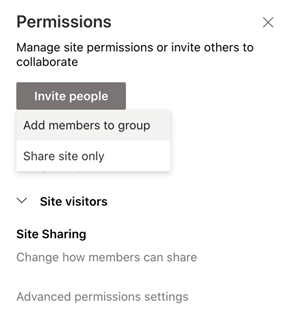
7. Now, I will click on Add members.
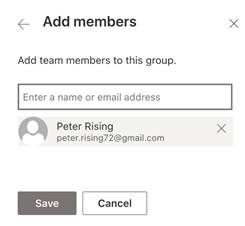
8. Here I will add my own Gmail email account, then click Save.
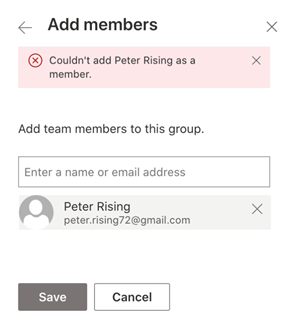
9. What happens is that you can’t add my Gmail account as a member due to the settings we defined in the General / HR label.
So, that’s how sensitivity labeling works with Site and Group settings within a SharePoint Online team site.
Summary
In this post, we’ve explained the principles of applying sensitivity labels at the container level within Microsoft 365. We showed you that there are currently three containers to which sensitivity labels can be applied. These are SharePoint Sites, Microsoft Teams, and M365 groups.
We demonstrated how you could modify an existing sensitivity label in the M365 Compliance Center and enable it for Site and group settings. We also explained you can configure this when setting up any new labels from scratch.
Finally, we showed how to apply the sensitivity label to the first of these three containers by setting up a new SharePoint Online Team Site.
In part two of this blog series, we will show you how to apply the sensitivity label to the two other container options: Microsoft Teams and M365 groups.
On-demand Webinar you should check out: How to Prepare for Office 365 License Renewal. Hosted by Microsoft MVP Paul Robichaux.



Is there a way to apply a default sensitivity label to all existing *and future* sites? For example, I want to disallow inviting guest accounts to all sites, then use a different label to allow it for approved sites.
You can certainly use PowerShell to assign a sensitivity label to all sites, and have a scheduled job to pick up new groups/sites and make sure that they’re assigned the right label (you can also define a default label for new groups/teams/sites in the label policy published to users).
You’d have to come up with a way to mark approved sites/groups for group access. Maybe one of the custom attributes available for groups would do the job.
BTW, this article might help: https://practical365.com/monitor-changes-sensitivity-labels-container-management/
Tony thank you, that link is really helpful. Are you aware of anything on the roadmap or something that exists today, available through a standard O365 E3 license, that could be used to prevent a group / team owner from ever inviting a guest account to a group that hasn’t been pre-approved for guest use?
The requirement is, once a guest account is in the tenant, it should only have access to groups authorized for guest access, and there should never be a way for a group owner to circumvent that control.
Hi Peter,
This is a great article!
Any thoughts if we are able to apply a label to a folder instead of container?
My use case is the following: Let’s say I have an HR container, containing several folders. I would like to classify folder one as “Personal information”, where we’ll collect all candidates data, personal accounts, etc, so any file placed by the HR in this folder will be classified as PII. Then I have folder two as “Confidential data” , where I keep contracts, salary information, etc. So I would like to classify everything in this HR fder two as confidential.
If this is not a direct out of the box solution I can implement, what would be your suggestions to do in order to support this use case?
Thanks a lot in advance!
Hi Peter,
i hope you’re doing well!
i have a question please how many sensitivity labels can you apply to a file saved to a Microsoft SharePoint Online site ?
You may apply only one label to a file at a time. You can change the label, but you can’t (and wouldn’t want to) apply two or more labels to the same file.
Hello, maybe this has already been asked here, but I couldn’t find it until now. How can I set a default label for all SPO sites via PO script?
How can I set the familiarity in SPO as a mandatory field?
Many thanks for the answers, Thorsten
Use the SharePoint Online PowerShell option.
Get all sites with template = Group#0
Set-SPOSite -SensitivityLabel Guid (the identifier of the label to set).
HI
does this mean when apply sensitivity label to the site , it will automatically applied on the documents in the site?
No. The label is for container management, not for protection of the content in the site.
No, there is no connection between the site label and labels applied to documents within the site. Two very separate things at the moment as Tony has stated already.
Hello Peter,
By the way, thank you for your book titled “Microsoft 365 Security Administration: MS-500 Exam Guide”. I have benefited a lot.
I want to ask again just to be sure because my mother tongue is not English 🙁
Can I publish a sensitivity label I created on protection.microsoft.com in AIP Policy named AIP_Global?
Hello, thanks for great article. I have a question. Very happy if you help.
Previous admin created 4 labels with AIP in Azure Portal. It distributed these labels under the policy called AIP_Global.
I have enabled unified labelling. So AIP_Global and labels created with AIP appear on protection.microsoft.com(Security and Compliance Center) portal.
Now, can I follow you and add the “HR” sensitivity label I created in the protection.microsoft.com panel to the policy named AIP_Global? Or do I need to create a new policy?
My goal is to work with a single policy. Would something like this cause problems?
Hi Burak, you may edit an existing label policy no problem and add the new label. Just be careful about the label priority as order is important. It should be placed in the list of labels in order of its settings.
Hello Peter,
By the way, thank you for your book titled “Microsoft 365 Security Administration: MS-500 Exam Guide”. I have benefited a lot.
I want to ask again just to be sure because my mother tongue is not English 🙁
Can I publish a sensitivity label I created on protection.microsoft.com in AIP Policy named AIP_Global?
Thank you so much for your kind words. It’s always nice to hear people have enjoyed the book. Working on another one right now!
Yes you may publish your label to your policy no problem at all.
Thank you for your quick response. I have one more question. How can I be Peter Rising? Does it have a formula? 🙂
Ha, you are most kind! However, the best formula I can recommend is to strive to be the best version of you. This is what I try to do. Comparison is the thief of joy, so if you focus on being the best you, then you won’t go far wrong my friend!
Great article/series!
Is there a way to use AIP or IRM to prevent users from copying OneDrive sync files to DropBox or other external targets? (Other than just turning off local sync)
thanks
Hi Neal,
If the content in the OneDrive is protected with rights management / AIP encryption, then it doesn’t matter where the document is. It can be synced, copied to a USB stick etc, and the protection will always travel with the file, and only those authorised will be able to open it with a valid M365 account.
Thanks for this great series Peter…much easier to follow than parsing through all of the MSFT docs pages on this topic.
The process of publishing labels and their policies is still pretty confusing though, and what the different choices do.
For example, I’ve had some labels/policies I’ve published that can be selected via the Site information panel and the label then appears on the home page (and in Teams). But another one with different settings (guest access, who it’s Published to) shows up in Site information but can’t be selected there, only from the SP Admin center Policies tab as you described. And even then it does not show up on the home page. Any idea why that might be the case?
Hi TFlint. So just to confirm I understand correctly – the label can be seen under the Sensitivity dropdown in the Site Information settings, but when you try and click on it, nothing happens?
Hello,
Tenant settings of SharePoint Admin Access Control must be kept as “Allow full access”, but the Conditional Access policy, that automatically created when we enabling “Allow limited” option, must be turned back ON.
So if we go to the SharePoint Admin Access Control and enable “Allow limited” -> Conditional Access policy created automatically with ON state;
If we go back and set option as “Allow full access” -> Conditional Access policy will be automatically disabled, then we need enable only Conditional Access policy.
This is needed, because if whole tenant will be set to the “Allow limited” option, then this tenant settings wins the “per site” Conditional Access settings 🙂 But Sensitivity Labeling works as “per site” Conditional Access settings, if you apply Sensitivity Label to site, then site receive this parameter (as example): Get-SPOSite -Identity https://contoso.sharepoint.com | FL ConditionalAccessPolicy
So for every site, that we apply label, the parameter “ConditionalAccessPolicy” will be set, but if we have applied “Set-SPOTenant -ConditionalAccessPolicy AllowLimitedAccess” then this is a Tenant level settings, then doesn’t matter what you have in the “per site”, tenant level settings will win…
Hi LightUpDiFire, yes good observations and you do indeed have to be very careful when applying that tenant wide setting from the SP Admin center, and be mindful that CA policies will automatically be created and turned on as a result. This probably needs a blog post all of it’s own actually. Might get working on that! Thank you.
Can we apply these sensitive settings for external users (Outside Organisation) so that they can not print, share, forward or save the documents. Only “Read Only”?
This is something that you can configure yes, but it’s within the Information Rights Management feature as opposed to sensitivity labelling. You can read more about this here – https://docs.microsoft.com/en-us/microsoft-365/compliance/set-up-irm-in-sp-admin-center?view=o365-worldwide and here – https://support.microsoft.com/en-us/office/apply-information-rights-management-to-a-list-or-library-3bdb5c4e-94fc-4741-b02f-4e7cc3c54aa1. Any more questions please just let me know!
What i miss is, can we apply a label on a existing SP site and how? Further im confused. If i assign a label to groupX does this mean only groupX gets Contributor permissions on the site? So labels are also some sort of authorization/permission settings? So What happens if groupA has read permissions on a SP site via SP permissions and we add a label with groupB and select Private will this block groupB users ?
Yes we can apply a label on an existing SP site. Select the Site in the SP Admin Center, then click on the Policies tab. Under Sensitivity, click Edit and you can choose the label to assign to the Site.
No, that action does not block the users with read access. They can’t share the site itself as a container object, but they can still work at a document level in the site with whatever permissions they have there. At the moment, the Site level and the document level are unrelated. No inheritance or anything like that.