Device Co-Management with Configuration Manager & Intune
How do we secure data accessed by multiple devices? Windows MVP Chris Rhodes discusses device co-management with Configuration Manager and Intune.
How do we secure data accessed by multiple devices? Windows MVP Chris Rhodes discusses device co-management with Configuration Manager and Intune.
Take a look at Azure ATP (Advanced Threat Protection), the cloud-based security service by Microsoft that provides monitoring and alerting for suspicious activity in your on-premises Active Directory environment.
How the latest reported Office 365 security vulnerability highlights the need for customers to use defense in depth and apply a layered security strategy to protect themselves in the cloud.
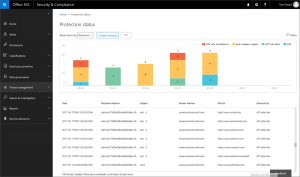
Learn how to use Office 365 and Azure security features to protect your organization's identities, endpoints, and information from security risks.
Microsoft has issued a security advisory to Office 365 customers about a security risk with the Azure AD Connect sync service account.
The Exchange Online Remote PowerShell Module uses an installation and update method that may leave your management computers exposed to security vulnerabilities.
Are Sender Policy Framework (SPF) records in DNS necessary for domains these days?
A permissions entry in Azure Active Directory user profiles raises questions about data sharing between LinkedIn and Microsoft.
Microsoft is rolling out a change from August 2017 for Azure Active Directory conditional access policies to begin applying to the Office 365 portal.
 3 Comments
3 Comments
Here's what is new and changed in Office 365 for June 2017.
How to configure a OneDrive for Business sync policy to restrict synchronizing OneDrive files to computers that are not joined to the domain.
Are you interpreting Microsoft security bulletins for Exchange Server and applying your patching policy the right way?