
Hearing that an organization is migrating from their on-premises to one Office 365 tenant is a business case study we’re all familiar with now. And although this is becoming standard practice for businesses wanting to become more cost-effective, secure and flexible there are still implications to consider with this move. For example, in my line of work, I often come across situations where a local Active Directory object should be migrated to different Office 365 tenants and I’ll explain the multiple reasons why this occurs.
Firstly, a common reason for this is that the organization has subsidiaries who still want to share the on-premise service, but also want to be independent of the cloud services.
Another scenario I’ve come across is when an association wants to migrate an Active Directory object to multiple tenants. For example, if you think about a sports association, these often contain multiple sports federations and only some of these have the rights to use Microsoft non-profit subscriptions. In the case I’m referring to, it makes perfect sense to have a dedicated Office 365 tenant. However, this is from a cloud perspective, in the on-premise site, all the federations are still in the same Active Directory, in one forest, divided into different OU’s.
Our third reason is that a global organization has some local legal specifications. It could be that users and/or services from one destination cannot be used from the same side as another local destination (country)
These three examples all have one thing in common: they require you to synchronize one AD Forest into multiple tenants. As per Microsoft’s requirements, only one AD object can be synchronized to one tenant at a time. Which we can execute by using Organization Unit (OU) segregation in Azure AD Connect which I’ll delve deeper into in this article.
Active Directory
The first step to fixing this request is preparing the on-premise Active Directory. At this stage, you don’t need to focus on the forest functional level, the requirements for this task can be found here. Instead, your focus should be on having a detailed concept of which OU needs to be synced to which tenant as this is required for the configuration of the Azure AD connect later. As I mentioned previously, the reason for this is that we’re only supported to synchronize one AD object (user, group) into one tenant at a time, so we have to the objects to satisfy this requirement.
In the next picture, I’ve provided an example of how our Active Directory structure should look:
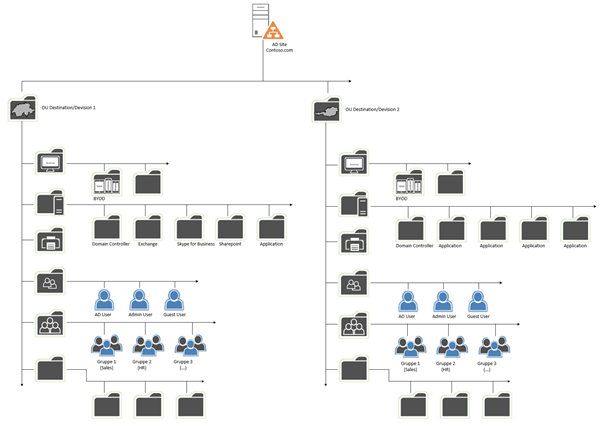
In this example, you can see a part of the Contoso on-premises Active Directory, and also two Destination OU’s “Switzerland” and Austria”. Each of these OUs contains sub-OUs with Users, Groups, etc. Here, we want to sync Users and Groups from the OU “Switzerland” to Office 365 Tenant 1 and Users and Groups from the OU “Austria” to Tenant 2.
Option one: Password Hash Synchronization (PHS) or Pass-through Authentication (PTA)
The supported solutions available to us are either Password Hash Synchronization (PHS) or Pass-through Authentication (PTA). To use either of these, you need to configure Azure AD Connect (AAD) in that way, so both tenants and the local Active Directory can be served from AAD servers. Later in this article, you’ll see how to configure the sync part of the local Active Directory OUs for each tenant. In the picture below, I’ve demonstrated how the design should look:
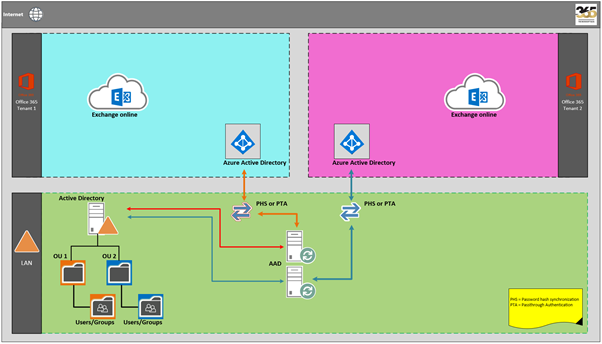
However, there is one very important point you must consider for this solution. If you use PHS or PTA, you’ll only be able to use SSO (seamless sign-on) for one of the two tenants. This means that you or the company must decide if Switzerland or Austria will be able to use SSO because whichever Destination OU SSO you don’t choose won’t be working. The reason behind this is the Kerberos Key exchange for the computer object AZUREADSSOACC can only be written for one tenant during the configuration of the SSO. However, if SSO is a must-have for both tenants, there is another solution to how this can be implemented.
Option two: PHS/PTA or Active Directory Federation Services (ADFS)
We discussed that there is an option to configure multiple Tenants with SSO on both sides. A supported solution for that request is to use it for one of the two sites PHS or PTA as described in the previous chapter, combined with SSO, and for the other Tenant an ADFS installation with or without PHS. This configuration structure will look like the picture below:
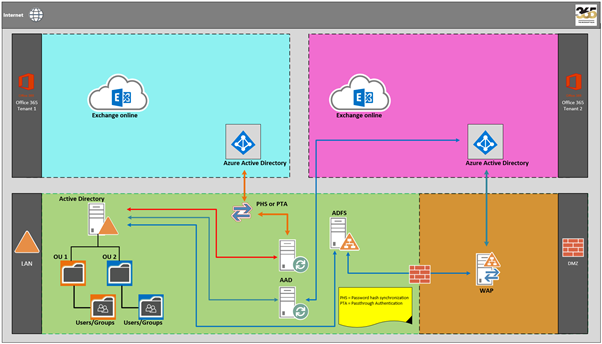
In the solution shown in the above diagram, Contoso has decided to configure the tenant for the Destination OU “Switzerland” with PHS or PTA with SSO and the Destination OU “Austria” with ADFS. In this case, Contoso can use SSO for both Tenants. The solution with ADFS needs a higher financial investment because you’ll need to install at least two ADFS and two Web Application Proxy (WAP) servers, two times load balancing, and certificates.
Of course, there is also a solution with DNS load balancing, but in this case, I want to show you the most foolproof solution because I don’t recommend DNS load balancing.
So, what do I mean by the “chance” being higher when using third-party services? Well, if you look at the two main OU’s in this article, I’ve written about “Destination OU’s”, however they can vary based on your scenario. For example, you could have one tenant for administration, office and back office materials, and the second tenant for trading.
Trading departments are known for needing at recurring intervals a very high calculation power. Using a third-party cloud solution would enable you to fulfill that need and it makes sense for the trading tenant to be configured the SSO with ADFS.
Exchange Online and Teams Implications
The two options we’ve discussed, PHS/PTA or ADFS, are the preferred solutions. However, there is a crucial point that we need to contemplate here. If the association in question uses Exchange Online, it will only be available for one of the tenants. Microsoft currently doesn’t have a solution to create an Exchange Hybrid to multiple Office 365 tenants. It also looks like there is a similar case with Microsoft Teams at the time of writing, the main difference here is if the association is using different namespaces, then all tenants are able to use Microsoft Teams.
Azure AD Connect
When you start the configuration of AAD, one of the first points during the Wizard is to choose the sign-in method for your Users. As you can see, the first three options are the ones, that I described in this article:
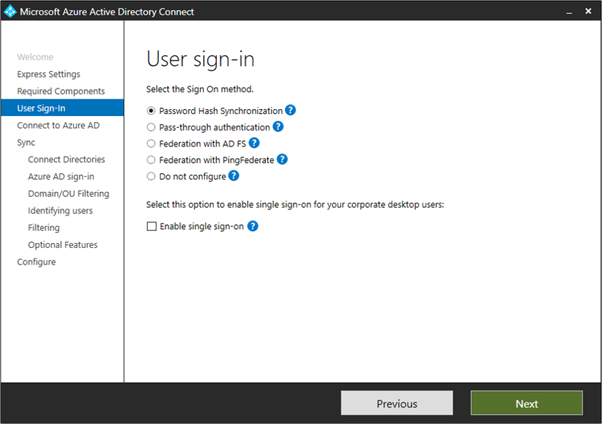
To be more precise, if you choose PHS that means users can sign in to Microsoft cloud services, such as Office 365, using the same password as their on-premises network. The user’s passwords are synchronized to Azure AD as a password hash and authentication occurs in the cloud.
If you decide to use PTA, users can sign in to Microsoft’s cloud services, like Office 365, using the same password they use in their on-premises network. The user’s password is passed through to the on-premises Active Directory domain controller to be validated.
In this article, we’ve also discussed the third option using ADFS where users can sign in to Microsoft cloud services, such as Office 365, using the same password they use for their on-premises network. The users are redirected to their on-premises AD FS instance to sign in and authentication occurs on-premises. In this case, PHS can also be used in combination as a backup solution and for credential leakage detection in Azure AD Premium.
During the AAD configuration you will arrive at Domain and OU filtering, at this point you need to decide which OU’s need to be synced to which Tenant, which we described earlier in this article in the Active Directory section.
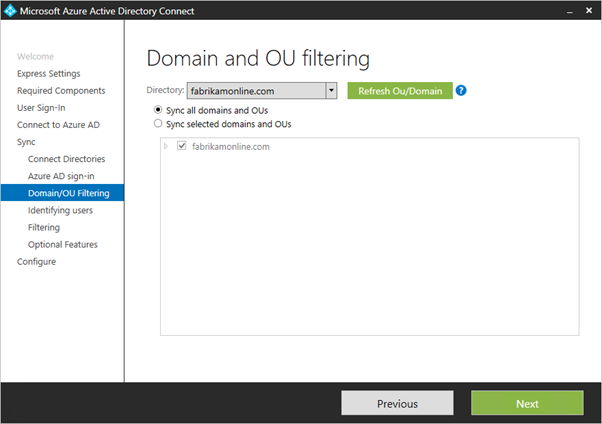
Note: If you’re using OU-based filtering with Azure AD Connect version before 1.1.524.0, new OUs added later are synchronized by default. If you don’t want new OUs to be synchronized, then you can configure it after the Wizard has completed the on-based filtering. For Azure AD Connect version 1.1.524.0 or later, you can indicate whether you want new OUs to be synchronized or not.
It’s also possible that some domains aren’t reachable due to firewall restrictions, consequently, these domains are unselected by default and have a warning.
Unreachable domains
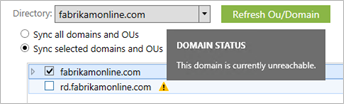
If you see this warning, make sure that these domains are definitely unreachable and the warning is expected.
If you’re not so familiar with the configuration of AAD, I recommend you check out the Microsoft Technet article about the custom installation of Azure AD Connect.
For this configuration, you’ll need to have two Azure AD Connect instances, one for each tenant because, as previously mentioned, you can’t synchronize into two tenants with one Azure AD Connect server.
Conclusion
When faced with this challenge, the first and foremost action you must take is establishing how the future solution must look. Do all your sites need SSO? And, do one or multiple tenants in the future need a third-party cloud solution such as Salesforce etc. which requires authentication?
Once you’ve got a clear idea of how this should look, the next step is to create the design and prepare the Active Directory and Objects that have to be synced. With good preparation, this can be performed swiftly. Previously in this article, we discussed the considerations that need to be made because some of the services can’t be used in the Cloud, such as Exchange Online, or only with different namespaces, such as Teams. These restrictions can cause problems later and therefore must be accounted for early on. It’s similar to SharePoint and it’s permissions.
Even if the on-premise Active Directory is shared, the two tenants are completely independent. If the cloud service can’t be shared or federated, all services (e.g. Fileserver) must be located on-premise.



Hi Drago…. Great article. I agree it is all about the OU planning and filtering. However, according to the latest Microsoft support article (newer than when you wrote the blog) Microsoft does now support “AADConnect can synchronize the users, groups, and contacts from a single Active Directory to multiple Microsoft Entra tenants. ” I am reading that we could synch the same user to two different tenants if we added an attribute or two to change the UPN suffix of one of the account synchs? Would you agree?
https://learn.microsoft.com/en-us/entra/identity/hybrid/connect/plan-connect-topologies
Hi Drago,
It’s a great article explaining how OU filtering can be used to separate AD objects to two AAD Tenanats. In our situation, we want to use Tenant1 for all users in the organization for all Microsoft 365 services and want to use Tenant 2 for only Microsoft 365 Sharepoint service for limited users. Is this possible to configure. Thank you.
Venu
Hi Drago
Excellent Article. I am not sure I understand the Exchange Online Part. So if we have a single Forest with the AD setup for Tenant1 and child domain for Tenant2 and implement ADFS for Tenant1 and PHS for Tenant2 using separate AADConnect instance, then only one organization can use Exchange Online service? What if the Organization is migrating from a non-Exchange Messaging platform, for example Groupwise? Will both Tenants be able to use Exchange Online? Please clarify.
I am seeing additional limitations of Single Forest with Multiple Tenants as shown by this document. Your article addresses the SSO workaround but I see more limitations discussed like GAL, W10 Device Registrations, Group & Device write-back, etc.
https://docs.microsoft.com/en-us/azure/active-directory/hybrid/plan-connect-topologies
How does that affect the planning if Multiple Tenants are a must? Will this require 3rd Party Identity as source instead of AD?
Hello, PS,
In general, Exchange only allows the combination of one environment (on-premise and EXO). If you have other third party tools in use, you can try to create them instead of MAPI as IMAP accounts on your EXO.
So you can create your users of the child on-premise domain on the EXO of Tenant 1.
Here are some infos about IMAP with EXO:
https://docs.microsoft.com/en-us/exchange/clients-and-mobile-in-exchange-online/pop3-and-imap4/pop3-and-imap4
Regarding your second point: W10 Device Registrations, Group & Device write-back, etc. this was well described by the Microsoft link, that you have posted.
How this affects your multi-tenant planning I can’t describe so quickly now, but this question would be worth an article.
Hi,
So my organization is looking to have a more robust SSPR capability and we are thinking about taking advantage of our current Azure ADFS environment. It looks as if this can easily be done for users that are say off-site to change locked passwords, but what about users on-site and only have the workstation login screen/credential provider? Is there a design where users can reset their passwords from their logon screen on-premise using Azure SSPR? Does there need to be an updated Credential Provider installed on the workstation?
Hello, Chris,
I can’t tell you much about it, as far as I know, there’s an on-premise integration.
Maybe this article will help you:
https://docs.microsoft.com/en-us/azure/active-directory/authentication/concept-sspr-howitworks
Hi Drago,
First of all, fantastic article, and thanks for the tips.
I have one question though when it comes to SSO across SaaS application.
When setting up SSO with third party application, on the SaaS application side, I usually can point only one IDP. If I have a SaaS application that need to allow both IDPs ( Tenant 1 and Tenant 2 ), what would be the best approach to this?
Thanks,
Hello, Gilles,
good question, I hope I got it right.
If you have external or on-premise applications, you can set them up (per tenant) with the Azure Application Proxy.
Take a look at this link:
https://docs.microsoft.com/en-us/azure/active-directory/manage-apps/application-proxy
I hope this helps you?
Thanks for this. Could you save images in a bigger size for the next articles? 600 pixcels is not that big with today screens 😉
Hi Alex, sure, I will try to deliver the images in a better size.