When a user in the organization has a mobile device configured for ActiveSync, Exchange Server 2010 gives them the capability to perform their own remote device wipes.
This is useful in scenarios such as a lost of stolen mobile phone, because the user can often perform the remote wipe faster than if they had to contact their IT support.
There are a few caveats of course.
The user needs to be aware that the capability exists, and either be trained or be able to access help documentation for the process. This means your user education needs to be performed in advance, or alternatively your help documentation needs to already exist and be available somewhere that you can direct the user if they contact you for support.
The mobile device also needs to make a connection to the Exchange server for the remote wipe to occur. There are a number of ways that a lost or stolen device may never contact the server again, such as:
- the device isn’t configured for push email, so doesn’t automatically connect to the server
- the thief disables 3G/wireless to prevent connections being made
- the mobile carrier disables the SIM card
- the user changes their password in Active Directory
- the device is blocked by a device access rule
So with all of that in mind, lets take a look at the process for a user-initiated remote wipe.
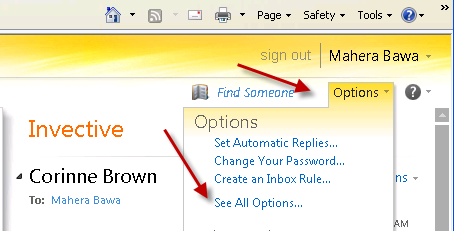
Exchange makes this functionality available to the end user via the Exchange Control Panel. Users can access the Exchange Control Panel by first logging in to Outlook Web App, clicking Options in the upper-right corner, and then choosing See All Options.
Clicking on Phone on the left-hand side displays the list of mobile devices associated with the user.
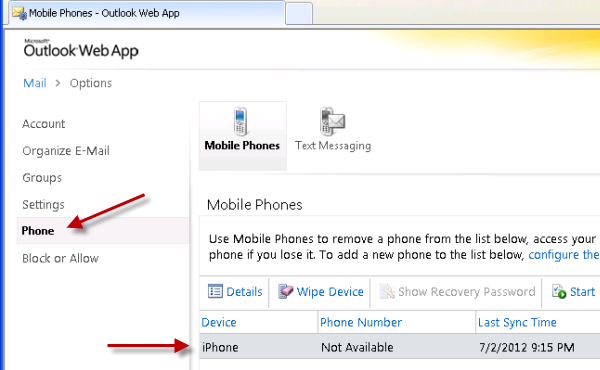
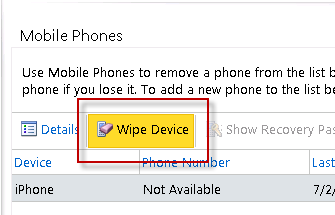
Select the device you wish to wipe and click on Wipe Device.
A warning box appears to confirm that the user wishes to wipe their device. Click Yes to confirm.
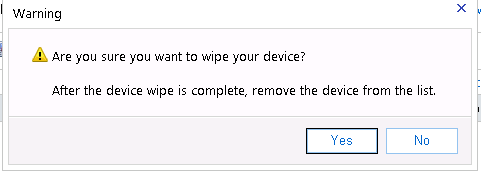
The device status changes to Wipe Pending. The user has the opportunity to cancel the device wipe before it completes, otherwise they can continue to monitor the status here.

The next time the device connects to Exchange (if it ever does), the remote wipe is initiated.
To the person in possession of the device there are no warnings or other messages before the remote wipe begins. In the case of the iPhone I’m using to demonstrate this, the device reverts to factory defaults and goes through the initial configuration steps when it starts up again.
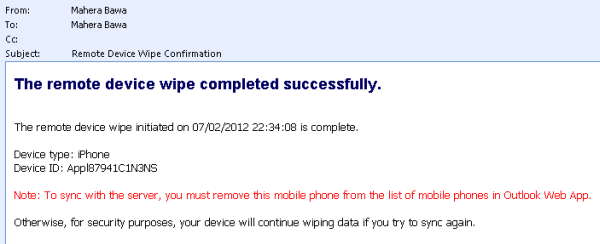
The user receives a confirmation email letting them know that the remote device wipe has completed.
They can also check the status of the wipe request in the Exchange Control Panel.
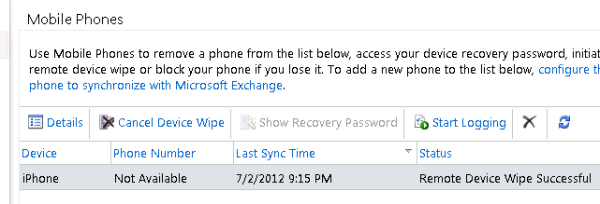
Finally, they can remove the device from their list of associated mobile devices by highlighting it and clicking the Delete button.

As you’ve seen in this article, Exchange Server 2010 puts some very useful and powerful mobile device management capabilities in the hands of end users, allowing organizations to give more control to their staff and relieve some of the burden from IT staff.
If this is something you’d like to see first-hand, but you don’t have spare mobile devices available, you can use virtual Android devices instead.



Hi Paul, useful insights here. How do I access the history of a Remote Device Wipe? Is it possible to get details of an IP/domain/hub or the like of where the request was initiated?
Hello,
Few days ago, I downloaded the Outlook App for Android and was able to sign in and sync my work exchange email account. Later on, I found that we are not allowed to connect to my work email remotely outside the network, so, due to policy, I am forced to delete the account and remote. Accidently, I only deleted the account without REMOTE, through settings in Outlook App. I went on OWA, to delete the phone associated with it. So, does this solve the problem of deleting the remote account? My company requires me to delete the remote account even from the external server that it stores the email data. I can’t wipe out my phone because I am still using it. So, just deleting the device (without wipe) will also stop the sync process with that device and delete all data stored in external server? is that correct?
Thanks,
Mo
Microsoft purges inactive account info from the cloud service after a short period. I think it’s 24 hours, maybe 48. Basically if you do nothing it should be fine.
Paul,
Hope this message finds you good..!!
Just checking to see if there is a way to find out who initiated Mobile device Wipe out request for a specific user?
Will both methods of doing the wipe send out email notification?
I think user-initiated will notify the user. Administrator-initiated will notify whoever the administrator specifies.
Is there a way to see and/or change what email address the ‘Administrator’ is for these notifications? I know who in our IT department is getting them but would like to change it so a group of Exchange techs get these emails…
When you run Clear-ActiveSyncDevice or Clear-MobileDevice in PowerShell you can specify a -NotificationEmailAddress parameter.
Sorry, I meant for user initiated wipe requests. Not everyone appropriate in our IT team is getting those, and I would like to fix it.
Pingback: Remote Wipe Doesn’t Work! | Exchange Source Book
Is there any technical difference between an ActiveSync device wipe performed by a user via their web console versus an Exchange/ActiveSync admin device wipe? Thanks
No real difference, both will wipe the device.
Pingback: Exchange 2010 Error “The ActiveSyncDevice Cannot be Found” When Performing a Remote Wipe | Andrew's blog of things
Hi Paul,
Thanks for this very helpful article. I’m just wondering if you were able to perform this device wipe on the ECP page instead of OWA? In my organization, this OWA seems to work as long as you have mailbox rights to the user receiving the wipe command.
But on the ECP Page > My Organization….managing a device of a user doesn’t seem to work. We get ‘Access is denied’ when saving after a Wipe Device is initiated. Please note that we already have the appropriate Role Group created for this as well.
Can you advise on the resolution of this issue? Thanks so much.
John
Are there more error details shown or does it just say “Access Denied”?
Yes, just ‘Access Denied’ error. should I be seeing more details of the error in checking IIS logs? I’ve explored that before already but it doesn’t give me any helpful information on this. I’m just thinking that there might be a missing role that we should assign to the role group we have created.
The role group we created is almost similar to this: http://blogs.technet.com/b/exchange/archive/2012/09/12/rbac-walkthrough-of-creating-a-role-that-can-wipe-activesync-devices.aspx
Basically our goal here is to have the security team of our organization be able to remotely wipe any user’s activesync device without having to log in to individual’s mailboxes through OWA (either a password reset or mailbox full access) so we have the best option of assigning them to this role group then perform the wipe through ECP managing the entire organization’s ActiveSync users but it’s not working. If you have a good solution or probably a better workaround on this, I would greatly appreciate it. Thanks Paul!
Did you ever figure this out, I have the same issue.
Pingback: "The ActiveSyncDevice Cannot be Found" When Performing a Remote Wipe
Hi Paul,
I love this feature of Exchange we have used it on several occassions… primarily for reissuing company owned phones in that they can get a fresh start. I was quite surprised Apple would allow Microsoft to use ActiveSync with the iphones to wipe it back to factory defaults.
I even love that even in the ActiveSync device password policy you can set a number of failed attempts before it wipes the device. A very nice security feature… although caution is advised. This option has a double edge sword, if you can’t remember your pin to unlock your phone, and you yourself exceed that number, bye bye phone data.
I do want to ask to see if you’ve come across this unusual situation. I posted a technet article a while back regarding the mobile wipe option. We have an issue where if a user syncs their mobile device with Exchange, and after the sync is made, we move that user to another OU. If it comes to where we need to wipe the phone, the mobile wipe fails (this is from the EMC). The error log says it can’t find the object because it’s looking for the original location where the sync occurred.
We can easily move the user back to the original OU and the remote wipe works.. or someone posted on my technet question that you can use EMS to point to the user with the full OU path and it will work (have not tested this yet).
Upon further investigation i ran a Get-ActiveSyncDevice and Get-ActiveSyncDeviceStatistics on a persons mailbox. The IDENTITIES came up different from each command. 1 pointed to the correct location of the user object, the other pointed to the original location of the user when the sync was first made. I’ve looked all through ADSI and could not find the original location anywhere on the the Device object itself or the ocntainer it resides in under the user.
It’s a very strange situation, I was wondering if you’ve encountered this and get your thoughts on it.
JB
I seem to remember reading that on TechNet recently.
My thoughts are that it sucks. But I’d say you’ve found part of the solution (or workaround) with the different result that each of those cmdlets gives you. I’ll dig into it a bit more, maybe there is a scripting solution to this or at the very lease a scripted report that can flag the ones that have been moved.
Hi Jonathan, try this and let me know how it goes:
https://www.practical365.com/exchange-2010-error-activesyncdevice-cannot-be-found-remote-wipe
Hi Paul,
Thanks for taking the time to look into this. I will do some testing with the scripts on this link and see what comes up.
Jonathan
My apologies for this being so long ago. Just FYI, The best solution is to script it in powershell as you stated in your link. I’ve had a lot of PowerShell to learn from the time I had this issue come up.
But just as your article states if you can pull the information of the actual location.. the full path, stick that in a variable, then run Clear-ActiveSyncDevice $devicePath. I had to set it up where a device had to be selected from a list and then give the user the option to either Wipe it or remove the partnership. Works like a charm.
PowerShell scripting has been a life saver on many tasks that i do.
Thanks again Paul!
JB