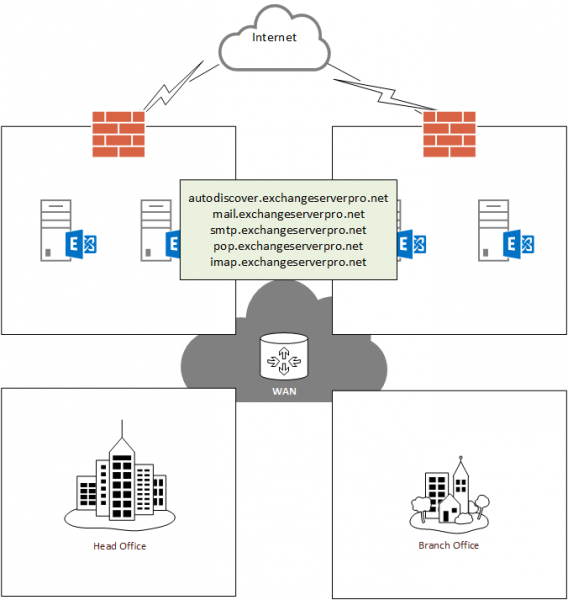
For this Exchange 2013 upgrade project a new SSL (SAN) certificate is being provisioned for the Exchange 2013 servers. From the namespace and certificate planning part of this series we know that the following namespaces are required for the certificate:
- autodiscover.exchangeserverpro.net (HTTP – Autodiscover)
- mail.exchangeserverpro.net (HTTP – Outlook Anywhere, OWA, ECP/EAC, ActiveSync, EWS, OAB)
- imap.exchangeserverpro.net (IMAP)
- pop.exchangeserverpro.net (POP)
- smtp.exchangeserverpro.net (SMTP)
Note: the Exchange 2010 SSL certificate can be re-used if it contains the correct namespaces. You can export the SSL certificate from Exchange 2010 and import it into Exchange 2013. However, if the names on the certificate are not correct, or the certificate is due to expire soon anyway, you may find it easier to simply acquire a new SSL certificate.
To complete the SSL certificate configuration the following process is used:
- Generate a Certificate Request for Exchange 2013
- Submit the certificate request to the CA to generate the SSL certificate. For real world production environments I recommend Digicert for their competitive pricing, good support, flexible licensing, and free re-issues if you happen to make an error. For the purposes of this demonstration a private CA is being used by following these steps instead.
- Complete the pending certificate request
- Export/import an SSL certificate to multiple Exchange 2013 servers
- Assign the SSL certificate to services in Exchange 2013
The same SSL certificate is used on both servers. So the certificate can be acquired for EX2013SRV1, then exported and imported for EX2013SRV2. You should not provision separate SSL certificates for Client Access servers that will be accessed by clients via the same namespaces.
In the next part of this series we’ll begin configuring the Exchange 2013 server roles.



Hi Paul,
the offical SSL cert in my Exch-2010 has both webmail.domain.com and localhostname.local. The internal VD-URLs of the Exch-2010 are set to localhostname.local and the external to webmail.domain.com. Split DNS is set up an webmail points to the local TMG.
If I use the Exch-2010 cert also on the new Exch-2013, I run into the problem that the new localhost of the Exch-2013 is not in the certificate, which is no problem anyway since using split DNS. Can I configure the VD-URL (both internal and external) of the Exch-2013 to webmail.domain.com without running into any problems during co-existence?
Also, TMG is going to be replaced with the WAP. If using the old ssl certificate is no option, I would simply use an internal certificate for the Exchange-2013 and a new SSL certificate inside my ADFS farm for WAP. Is it a problem when I use webmail.domain.com in an internal on the Exch-2013 and in the official SSL-Cert on the Exch-2010. Any pointers? Thanks!
Pingback: Exchange 2010 to 2013 Migration – Configuring Client Access Servers
Thanks