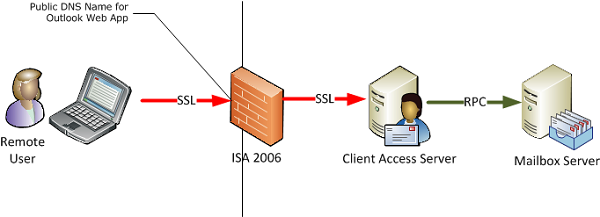
One way to make Exchange Server 2010 Outlook Web App (OWA) available for remote users is to publish it using ISA Server 2006. There are several parts of this solution that make it work.
- A public DNS name for Outlook Web App (in this example mail.exchangeserverpro.net is used)
- An ISA Server 2006 (with Service Pack 1) firewall configured with an external interface and IP address corresponding to the above DNS record
- An SSL certificate for Exchange Server 2010
- Exchange 2010 Client Access and Mailbox servers deployed in the organization
This diagram provides an overview of how Outlook Web App is published using ISA Server 2006. The remote user makes a connection over HTTPS (SSL) to the ISA firewall, which then reverse proxies the traffic over SSL to the Client Access server. The Client Access server is then responsible for proxying the requests for the user’s mailbox to the appropriate Mailbox server using RPC connections.
Configuring the Exchange 2010 Client Access Server
In this example the /OWA virtual directory on the Client Access server is configured for both Basic and Integrated authentication. This combination allows internal, domain-joined computers to seamlessly log on to Outlook Web App while also permitting the ISA server to use Basic delegation to authenticate the remote user.
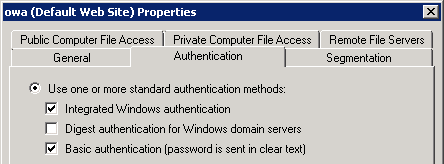
For more details see this article on how to configure Outlook Web App authentication.
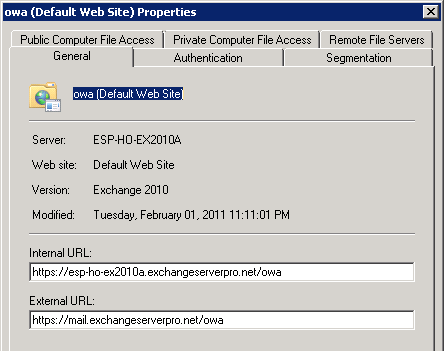
The Client Access server /OWA virtual directory has also been configured with the external URL to match the public DNS name.
The Client Access server also needs to be configured with an SSL certificate. Preferably this SSL certificate is from a public certificate authority but it can also be a private CA, as long as it is one that the ISA server trusts so that ISA considers the certificate to be valid. You can of course import root certificates to make just about any certificate trusted by ISA but it is less effort and a better overall solution to use a public CA.
Configuring the ISA Server SSL Certificate
The ISA server needs to be configured with an SSL certificate to accept the secure remote access connections. Although you can issue the server with its own certificate for this purpose you could also export the SSL certificate from the Client Access server and import it to the ISA server, provided that the license terms your issuing CA allow for that. Digicert is an example of a CA that allows certificates to be installed on multiple servers.
For more details see this article on exporting an SSL certificate from Exchange 2010 (note that it refers to importing it for Exchange 2003 but the steps are the same for importing to an ISA Server 2006 firewall running on Windows Server 2003).
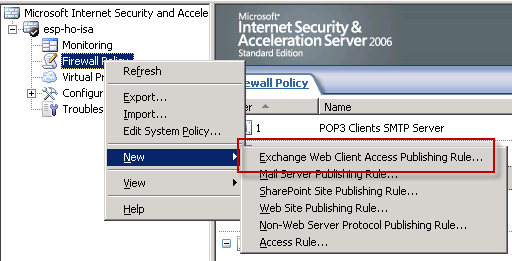
Configuring the ISA Server Publishing Rule for Outlook Web App
In the ISA Server Management console right-click the Firewall Policy and choose New -> Exchange Web Client Access Publishing Rule.
Give the new rule a name and click Next to continue.

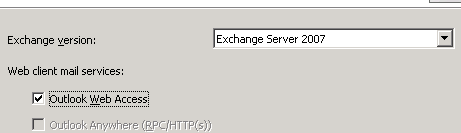
Set the Exchange version to Exchange Server 2007 (yes this is correct for Exchange 2010 publishing) and tick the box for Outlook Web Access, then click Next to continue.
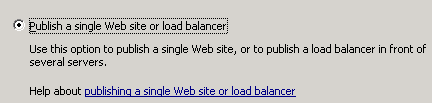
In this case a single server is being published. Click Next to continue.
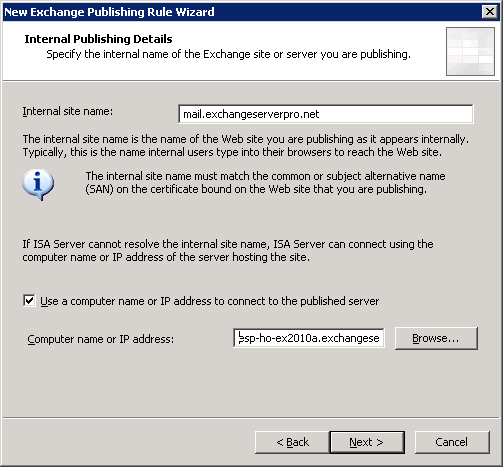
Enter the internal site name for OWA (in this case mail.exchangeserverpro.net), and optionally enter a computer name or IP address for ISA to connect to if the internal site name does not resolve in the internal DNS zone. Click Next to continue.
Configure the public names that this rule should accept connections for and click Next to continue.

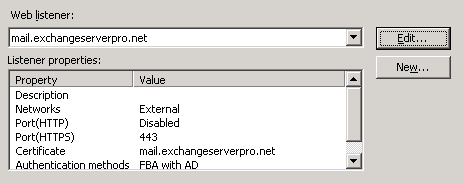
Now we need to configure a web listener to accept the remote user connections. Click on the New button.
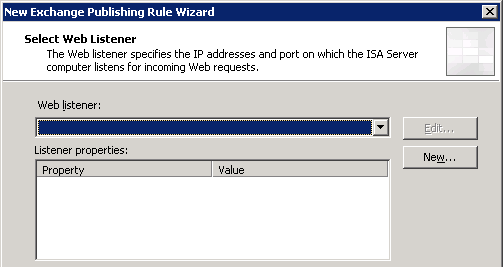
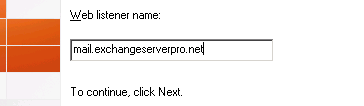
Give the new web listener a name and click Next to continue.
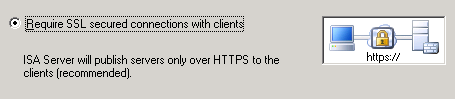
Leave the default choice to require SSL and click Next to continue.
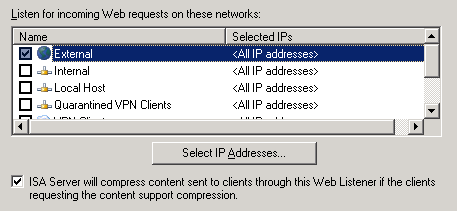
Select the External interface for the web listener to listen on. If your External interface has multiple IP addresses you can configure the web listener to listen on all, some, or just one of those IP addresses. Click Next to continue.
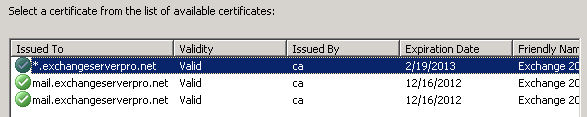
Click on the Select Certificates button.
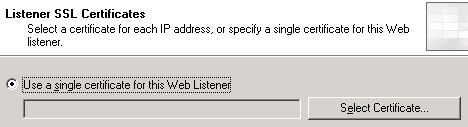
A list of valid certificates will appear, which should include the one you imported to the server earlier. Choose that certificate and click the Select button, then click Next to continue.
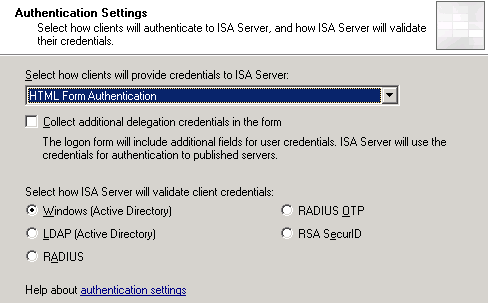
Leave the authentication set to HTML Form Authentication and Windows (Active Directory). Note this assumes your ISA server is joined to the domain, otherwise you can configure LDAP authentication. Click Next to continue.
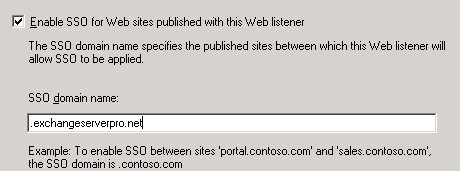
Single Sign-On is useful but optional. Click Next to continue.
Click Finish to complete the new web listener wizard. If there are no warnings or errors displayed click Next to continue.
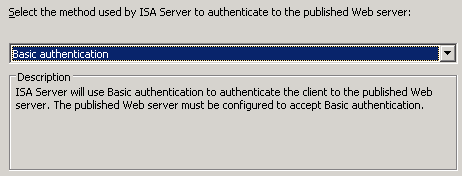
Leave the authentication delegation set to Basic Authentication and click Next to continue.
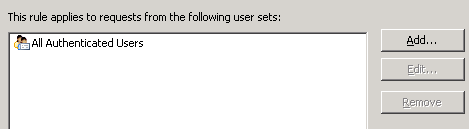
Leave the users set to All Authenticated Users and click Next to continue.
Before you click Finish to create the new rule first click on the Test Rule button to validate the settings you chose.
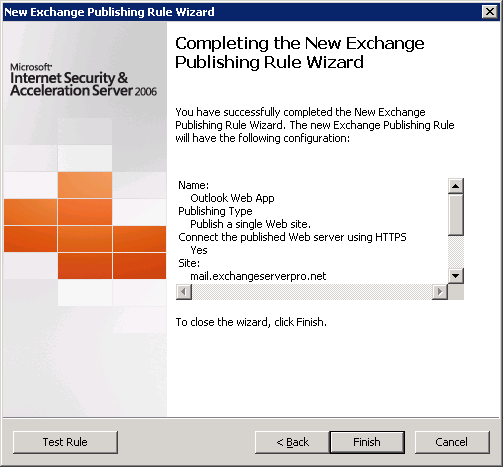
If the tests are all successful click on Close and then Finish to create the rule.
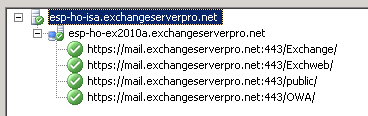
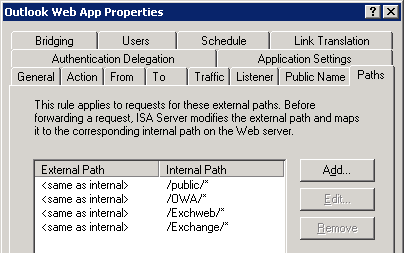
Before applying the changes to the Firewall Policy double-click the new rule to open its properties. Select the Paths tab and then click Add.
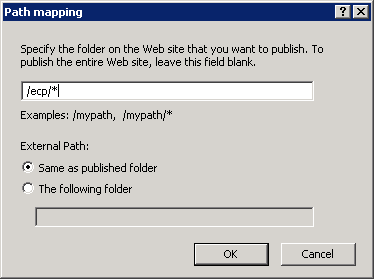
Add the Exchange Control Panel virtual directory path of /ecp/* and then click OK and OK again.
Now click Apply to commit the changes to the Firewall Policy.
Testing the ISA Server 2006 Publishing Rule for Outlook Web App
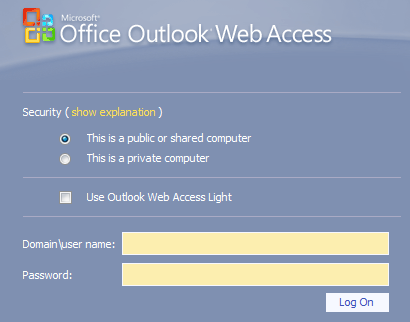
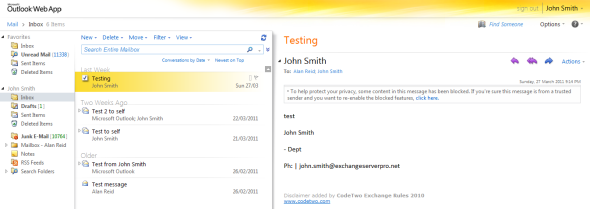
Now that the rule has been configured we can test it from outside of the firewall using a web browser. When the remote user first connects to the Outlook Web App URL they will see the Exchange 2007 style log on form that ISA 2006 renders.
However after logging in the Exchange Server 2010 Outlook Web App interface will be available to the remote user.




Hi,
after setting up isa server 2006 how to make it a proxy server ?
and is the ip of the proxy server is the same as the server ip itself ?
Thanks.
Thanks a lot !
If I place a Edge Transport Server between two ISA Servers, in a DMZ, … Does the public ISA Server have to publish the OWA pointing to the Edge Transport Server or to the internal ISA Server ?
Hi Paul,
Excellent article by you as usual….!!!
I have want to ask that I have a firewall before my ISA Server 2006 .
On the firewall I have NATed the public interface with the private IP of my
ISA Server 2006.
Do I need to change some settings on my firewall also….???
Pingback: cb passive income license review
Pingback: google sniper 2.0 review warrior forum
Pingback: diabetes protocol reviews
Pingback: venus factor reviews
Hi Paul,
I have a issue i have exchange 2007 and isa 2006 everything was working fine suddenly when i try to login through browser to exchange in internal lan i cannot go through where as when i try it i get the login screen and i can login and browse mails.
can you give me any solution.
I hav already created roles in isa for owa and web listener.
Thanks.
Hi Paul,
I am process of migration rom exchange 2007 to 2010. We had also two exchange servers 2010, main exchange server (exchange server 1) had role (CAS, HT and mailbox) with sp1 and other exchange 2010 (exchange server 2 with no Sp1) who had only mailbox role.
I will like to remove mailbox (exchange server 2 with no Sp1) exchange server. Yesterday I had unmounted databases at exchange server (exchange server 2 with no Sp1) and stop the exchange services include exchange AD topology service, www publishing service and Net. Tcp port sharing/adapter services. When I had stopped these services I got warning at our main exchange server (exchange server 1 with sp1) (Microsoft exchange mailbox replication and still getting warning until I had started services at (exchange server 2 with no Sp1).
Here is following warning.
The Mailbox Replication service was unable to determine the set of active mailbox databases on a mailbox server.
Mailbox server: mailbox.exchangeserver.com
Error: MapiExceptionNetworkError: Unable to make admin interface connection to server. (hr=0x80040115, ec=-2147221227)
Diagnostic context:
……
Lid: 10648 dwParam: 0x6D9 Msg: EEInfo: Generating component: 2
Lid: 14744 dwParam: 0x6D9 Msg: EEInfo: Status: 1753
Lid: 9624 dwParam: 0x6D9 Msg: EEInfo: Detection location: 501
Lid: 13720 dwParam: 0x6D9 Msg: EEInfo: Flags: 0
Lid: 11672 dwParam: 0x6D9 Msg: EEInfo: NumberOfParameters: 4
Lid: 8856 dwParam: 0x6D9 Msg: EEInfo: prm[0]: Unicode string: ncacn_ip_tcp
Lid: 8856 dwParam: 0x6D9 Msg: EEInfo: prm[1]: Unicode string: mailbox.exchangeserver.com
Lid: 12952 dwParam: 0x6D9 Msg: EEInfo: prm[2]: Long val: -1988875570
Lid: 12952 dwParam: 0x6D9 Msg: EEInfo: prm[3]: Long val: 382312662
Lid: 24060 StoreEc: 0x80040115
Lid: 23746
Lid: 31938 StoreEc: 0x80040115
Lid: 19650
Lid: 27842 StoreEc: 0x80040115
Lid: 20866
Lid: 29058 StoreEc: 0x80040115
Next day I had just started all above mentioned services at (exchange server 2 with no Sp1).
exchange server. At (exchange server 2 with no Sp1) did not initialized the exchange management console because (exchange server 1 ) is installed sp1 of exchange server, but (exchange server 2 with no Sp1) is has no exchange SP1. Its give me following error at exchange management console. (connecting to the remote server failed. Cannot contact to this server because incompatible, current version 14.1.218.15. for more information see information about_remoe_troubleshooting).
Can you let me know if there is no problem I can uninstall or remove from control panel (exchange server 2 with no Sp1) exchange server from exchange environment (exchange server 2 with no Sp1 has no mailbox at its databases), and will it not effect to main exchange server 2010 sp1 (HT,CAS, mailbox).
Thanks in advanced.
Best regards,
Imran
I found these links
http://support.microsoft.com/kb/2633193
http://www.petenetlive.com/KB/Article/0000340.htm
I guess, the question remains, are these paths (Exchange, Exchweb and public) necessary on a Exchange 2010 environment? I’m fairly sure they were required on Exchange 2003 and 2007 but not sure about 2010
Anyone? Cheers!!!
It’s been a while since I set up an ISA or TMG for Exchange publishing and I don’t even have one in a lab I can check against, sorry.
From memory I published all of the various paths when setting up TMG.
Hey Paul, got a question regarding OWA Publishing Rule using ISA or TMG
A user reported issues with webmail and I started doing checks, when testing the OWA rule I was getting the following for 3 paths
Exchange, Exchweb and public
Time reported by the Microsoft Forefront TMG Firewall Service: 0.009 seconds
Testing https://outlookwebmail.company.com:443/Exchange/
Category: General error
Error details: An unexpected response was received from the server. HTTP response: 500 Internal Server Error
Action: Verify that the intended server is published and that virtual directories exist. Ensure that you can browse the published site directly from an internal client computer.
Note:
The virtual directories exists but when checking
Authentication on the virtual directory I get “There was an error while performing this operation” error in line 37 of the web.config file. Error: Configuration section not allowed to be set below application
HTTP Redirect was not enabled or configured so I enabled it with Redirect requests to this destination /owa
Now, the rule seems to be fine
Time reported by the Microsoft Forefront TMG Firewall Service: 0.005 seconds
HTTP response: 302 Moved Temporarily
The test successfully completed for this URL.
I’m not 100% sure about the correct setting for these 3 directories so I wanted to double check with you guys!
Thanks so much!!!!
Hi Paul,
Our comany had two exchange servers ( exchange 2007 and exchange 2010). We would like to use both exchange server work as client access and able to access the OWA with different public IP address (different external URL at OWA virtual directory).
Is it possible and how ?, we are using TMG firewall.
Best regards,
Imran
Great work
Dear Paul,
I have also a problem with two two authentication screens.
My setup is like this.
I Use Form authentication
mail.abc-as.dk ISA 2006 Exchange 2010 (mail.abcas.dk)
As you can se the domain are not the same for the external and the internal
The explanation you gave earlyer I do not understand.Can you give a littel more help.:-)
Thanks
Henning
Dear Paul,
Publishing Outlook Web App with ISA 2006 is a quite strait forward and easier because you can test it directly. But how about publishing Outlook Anywhere (RPC over HTTP)? Here is also auto-discovery and other nasty bits to consider. We for example already set-up and configured Outlook Anywhere access to our CAS servers. However because they face the internet directly (over a not very stable network link), we want to reduce the attack surface and do load balancing using an ISA server in front. I think it should be easy to achieve, but it is not! In fact, Outlook Web App works fine but not Outlook Anywhere! Looking forward for your tutor on this stuff and thanks in advance.
BTW, your tutors are great, well written and clearly introduced! Well done.
Hi Paul, 1. I too get similar two auth like Jorge, Is there a simple way other than creating second owa directory ? 2. How do i direct my site https://mail.abcde.com to https://mail.abcde.com/owa automatically when hey click ! Thanks mate.
Hi there,
1) No, that is how it is done.
2) You can simplify the OWA URL for your users following this advice on TechNet:
http://technet.microsoft.com/en-us/library/aa998359.aspx
Pingback: The Mailbox You're Trying to Access Isn't Currently Available
Pingback: Возможно вы незнали, что … » Архив Блога » публикуем Outlook Web App в ISA Server 2006
Hi, I have issue in this setup where I want internal network and external network to be presented with form authentication… however, when logging in user gets two authentication screens, first ISA’s then Exchange 2010’s is there anyway to have only a single authentication screen? Thank you
Hi Jorge, create a second OWA virtual directory (http://technet.microsoft.com/en-us/library/bb123752.aspx) on a second IIS website running on a different IP. Configure that one for Basic/NTML auth and publish it using ISA, and configure the other one for forms-based auth and use internal DNS to direct internal clients to that one.
I don`t know how to thank you!!
Pingback: How to Publish Outlook Web App with ISA Server 2006 « HeelpBook
Excellently Done….! Thanks