Need for Protection (and Good Security Defaults) Evident in the Cloud
One of the lessons learned from last year’s Hafnium fiasco was that some organizations with on-premises Exchange servers don’t manage them very well. This is acceptable when the servers aren’t exposed to the internet. It becomes potentially disastrous and a one-way ticket to compromise when they are.
As you might have heard once or twice before, things are different in the cloud. Microsoft manages servers and takes care of basic maintenance and other matters of server hygiene. Secure servers are good, but user account compromise still happens to give attackers a route into Office 365 tenants. Which is why Azure AD Security Defaults exist.
Azure AD Security Defaults for All
In October 2019, Microsoft enabled Azure AD Security Defaults for new tenants. In a nutshell, this means that accounts in those tenants use multi-factor authentication (MFA) unless administrators decide otherwise. MFA is goodness. Even MFA based on SMS messages is so much better than basic authentication with username and password. Combined with conditional access policies, MFA erects a substantial barrier against account compromise.
In a May 25 post, Microsoft announced the extension of Security Defaults to protect tenants created before October 2019. Microsoft says that the 30 million tenants currently protected with Security Defaults “experience 80 percent less compromise than the overall tenant population.” Implementing MFA is a big step forward. According to Microsoft, “When we look at hacked accounts, more than 99.9% don’t have MFA, making them vulnerable to password spray, phishing, and password reuse.” The popularity of password spray attacks against older email connection protocols like IMAP4 and POP3 is a big reason why Exchange Online will decommission basic authentication for these protocols (and five others) starting on October 1.
Microsoft says that rolling out Security Defaults to older tenants will protect 60 million additional accounts from attack. Given Microsoft’s latest number for Office 365 users (345 million paid seats), that number might seem low. However, it’s the number of unprotected accounts in older tenants – many older tenants use MFA and conditional access policies already. The focus is on extending protection to tenants that might not have the IT capabilities to implement better security practices. Microsoft explicitly mentions that they will target “those [tenants] who haven’t changed any security settings since deployment.”
Engage with Microsoft 365 experts like Tony Redmond at The Experts Conference 2022 in Atlanta, GA September 20-21.
The Big Roll-Out
Microsoft says that the roll-out of Azure AD Security Defaults to unprotected tenants has started. Initially, they are focusing on “customers who aren’t using Conditional Access, haven’t used security defaults before, and aren’t actively using legacy authentication clients.” It’s the same solve the problem in easy bites approach that the Exchange Online team is using to eradicate basic authentication: process the easy tenants first, then slightly harder, and gradually work through the installed base until you reach the most difficult tenants.
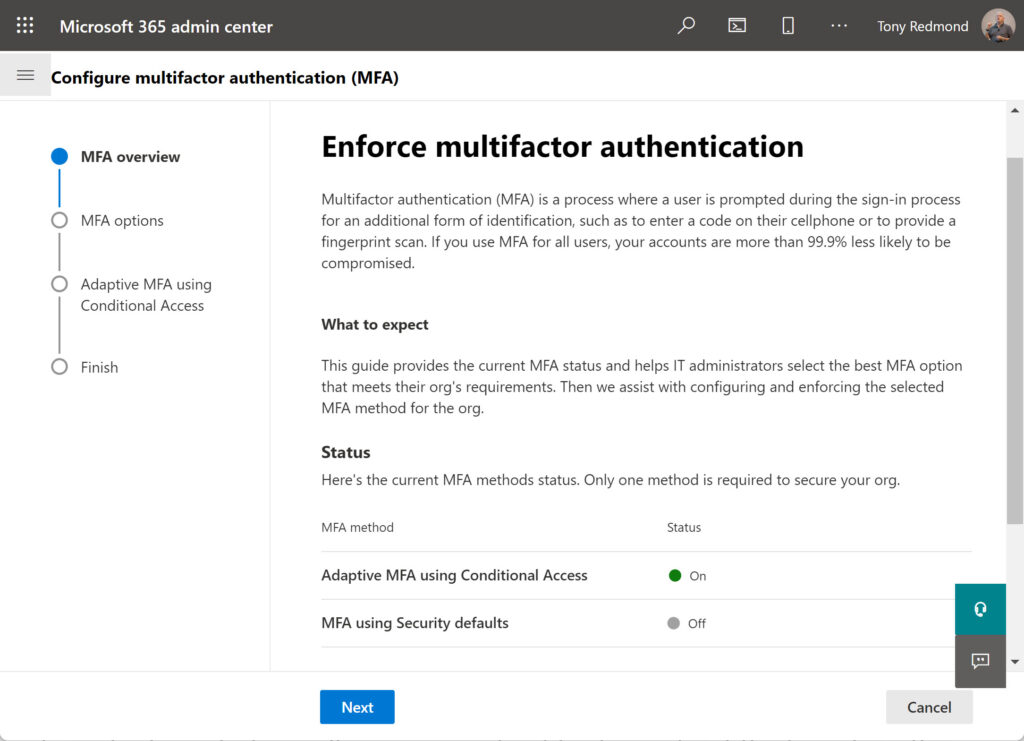
Tenant administrators will receive email notifications about the transition. Beginning in late June, administrators will begin to see prompts to enable Security Defaults when they sign in. At this point, they can choose to delay for up to 14 days or opt not to use Security Defaults by amending settings in the Azure AD admin center or Microsoft 365 admin center. In Figure 1, you can see that my tenant uses “adaptive MFA,” which is a pretty name to say that conditional access policies require MFA in certain conditions.
Enabling Security Defaults means that Azure AD will ask users to enroll for MFA, preferably using the Microsoft Authenticator app on a mobile device as the second authentication factor.
Cloud Security is Different
On-premises security needs, tactics, and techniques are different to what’s required in the cloud, but when attackers come calling, you must be able to repel them using appropriate tools. I think extending Security Defaults to all unprotected Office 365 tenants is an excellent idea that should help people escape the horrors of something like a business email compromise attack. Having an Azure AD account compromised is bad, and if it’s an administrator account, it could be as bad as having an on-premises server penetrated by something like Hafnium.
Alex Weinert, Director of Identity Security at Microsoft (who will speak at the TEC 2022 in-person event in September), says that the rollout will deliver “a massively improved security posture against Identity-related attacks.” Let’s hope that he’s right!
Engage with Microsoft 365 experts like Tony Redmond at The Experts Conference 2022 in Atlanta, GA September 20-21. Ask your questions 1:1, get hands-on in our M365 Managements Shortcuts Village, and network with peers!



