Pay As You Go for Microsoft 365 Backup
It’s clear that Microsoft 365 backup is a complex area. The lack of suitable APIs make backup difficult and restore impossible for some workloads, a fact that begs the question if Microsoft 365 backups are needed? Some organizations need backups (or think that they do), others use inbuilt features like Native Data Protection in Exchange Online, Restore this library in SharePoint Online and OneDrive for Business, and retention policies to retrieve data when necessary.
Some customers have asked that Microsoft take a more proactive stance and deliver backup and restore functionality for Microsoft 365. This is an understandable ask because it’s reasonable to consider backup and restore to be part of a complete end-to-end service. Until recently, Microsoft has avoided any discussion around backups and depended on ISVs to satisfy customer demand.
A new backup and restore service delivered as part of their Syntex content management suite marks Microsoft’s first foray into backup and restore for Microsoft 365 services.
PAYG Backup and Restore for Exchange Online, SharePoint Online, and OneDrive for Business
Microsoft’s announcement at the Ignite 2022 conference said:
“Whether you need malware protection or preserved file copies from a particular point in time, Syntex backup can help. It preserves the state of your cloud—across Syntex, SharePoint, OneDrive, and Exchange—so that you can get back to information from the last quarter, the last month, or the last decade with ease, keeping your backup stored conveniently in the Microsoft Cloud. Your backup is highly available and tightly integrated with your content policies.”
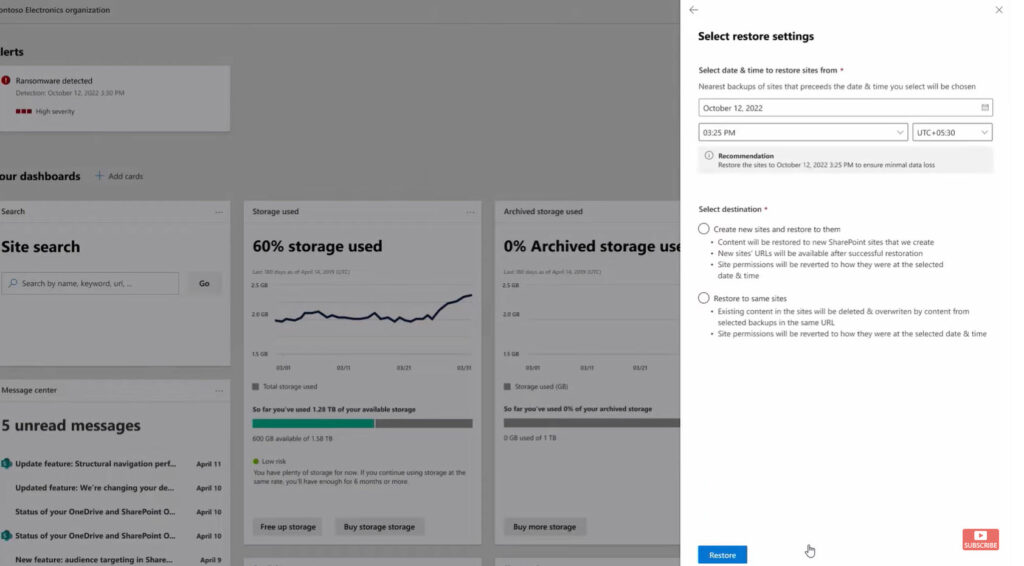
Additional insight is available from the Microsoft Mechanics session where Omar Shahine, Corporate VP for OneDrive and SharePoint, discusses their plans (watch the complete show or move to 10:50 in the timeline). Figure 1 comes from that session and shows the UX for restoring SharePoint sites after a cyberattack.
What I got from the session is that Microsoft plans to introduce Pay-as-You-Go (PAYG) backup and restore for Exchange Online, SharePoint Online, and OneDrive for Business. Customers will pay for the resources consumed for their backup and restore operations using an Azure subscription. There’s a lack of detail available about likely costs and functionality. More will be known once Microsoft makes the backup and restore functionality available in public preview.
On Demand Migration
Migrate all your workloads and Active Directory with one comprehensive Office 365 tenant-to-tenant migration solution.
Reasons Why You Should and Should Not Consider Microsoft Syntex Backup and Restore
Many reasons exist why Microsoft is a logical provider for backup and restore services. Among those reasons are:
- The Exchange, SharePoint, and OneDrive data resides in Microsoft data centers. Generating copies of that data for backup purposes should be much faster than streaming data across the internet to a third-party data center.
- Microsoft understands the data structures and controls the APIs to access the data for backup and restore. As such, they should be able to guarantee 100% fidelity when it comes to restoring data. Microsoft control over backup APIs is not necessarily a good thing, as demonstrated in their push to get ISVs to use the metered Teams Export API instead of Exchange Web Services to backup Teams data.
- Unlike third-party solutions, Microsoft can change the way that their applications work to make their backup and restore technology work better. For instance, Microsoft could retain documents of SharePoint and OneDrive documents when customers don’t enforce retention policies. The Microsoft 365 substrate already preserves “digital twins” of items from different workloads to enable common services like search to work smoothly. This is an example of how total control of an infrastructure allows a service provider to manage data to suit their needs (to be fair, the substrate also delivers enormous benefits to customers).
- The economics of scale within Microsoft’s data center operations should deliver lower costs. Whether Microsoft chooses to price accordingly is another matter.
Reasons Why Not to Use a Microsoft Backup Solution
The reasons why a Microsoft backup solution might be a bad choice for a Microsoft 365 tenant include:
- Monoculture, or putting all your (data) eggs in the one (Microsoft) basket. Depending on the regulatory environment a company operates under, they might be required to maintain separation of backup data from operational data.
- Microsoft doesn’t have a lot of experience with the delivery of backup and restore services. They don’t have a track record in this space and some similar technology like SharePoint’s Restore this library suffered horrible scalability problems when exposed to the imperfect world of customer operations. ISVs who specialize in this area might be able to deliver a better service, especially when things go wrong, and customers need urgent hands-on knowledgeable support to bring services back to an operational state.
- Cost. No one knows what charges will accrue under Microsoft’s PAYG scheme. Backup and restore could become a very competitive market when ISVs realize what they need to do to win business in terms of cost. Microsoft is likely to provide tools to estimate how much an organization will be charged for backup and restore, but the true cost of any PAYG solution only becomes apparent when you use it.
- The Azure subscription could become a potential single point of failure for backup operations. For instance, we don’t know what will happen under relatively common conditions like a credit card linked to a subscription expiring or exceeding its credit limit. Having some Microsoft Sentinel ingestion or reporting terminate because of an expired subscription is one thing; backups failing or being unable to restore data is quite another.
Being able to use a single vendor for all backup and restore operations can be quite a compelling proposition. Microsoft’s offering is limited to the two base Microsoft 365 services (email and document management). Microsoft’s move to bring the storage of files generated by applications like Stream and Whiteboard into SharePoint and OneDrive for Business means that the potential gap is smaller than it once was. However, gaps still exist in applications like Planner, Yammer, Project, and Power BI. ISVs might be able to offer broader coverage of Microsoft 365 data and third-party applications.
It’s possible that the sales tactic for Syntex will be to offer a complementary service to what customers already use. One obvious tack is to emphasize the speed of recovery that’s possible because the Microsoft backup data is already available inside their data centers. If a cyberattack occurs, customers should be able to recover back to a point in time faster than is possible with third-party solutions. In effect, customers could buy Syntex as insurance, something that gives them additional options should they need to restore data for any reason.
Protected Content
Files protected by Microsoft Information Protection (sensitivity labels) pose a difficulty for ISV backup products. SharePoint Online stores protected files in an unencrypted form to allow services like indexing and search to work against the content. When users or applications download files, SharePoint encrypts the objects. According to a discussion in the MIP Yammer network, the files are “encrypted with a different symmetric key every time so that they won’t be identical to the file at rest or previously downloaded copies.” If a backup product relies on hash values to check that the online and downloaded files are the same, it will fail for encrypted files. The processing of items protected by sensitivity labels is further complicated by options like double-key encryption and user-assigned permissions.
It might be that a backup product could simply copy encrypted blobs and leave it to applications to sort things out following a restore. For instance, a tenant administrator can use super-user permission to remove encryption from protected files with a PowerShell cmdlet. This assumes that the cmdlet can process the restored files (another thing to test!).
Given the relatively low percentage of tenants that use sensitivity labels, backup providers might have felt safe in ignoring the problems involved in processing encrypted content. This situation is gradually changing as Microsoft builds out the ecosystem around sensitivity labels. Protected content is usually the most confidential and valuable to an organization, which means that it merits consideration for backups.
I don’t know if the Syntex backup solution can deal with encrypted content (mostly Exchange messages and Office and PDF documents stored in SharePoint Online and OneDrive for Business). Because it’s a Microsoft solution, you might assume that Syntex can cope with all elements of the Microsoft 365 ecosystem, or at least it will work when tenants use a Microsoft-managed key for their encryption. If so, supporting encrypted content is another advantage for Syntex. If not, Syntex is simply doing what other backup solutions do.
The long-term solution is likely to be a supported backup/restore API that handles encryption and decryption when extracting items from repositories.
Wait and Test
Of course, everything depends on the technical details of the Syntex solution and how it fits into customer operational processes. It takes a lot for an organization to move away from a backup and restore solution that’s embedded and working well, especially to something that offers limited coverage of Microsoft 365 data. For that reason, I think the Syntex solution is interesting and worth considering when it is available, but likely to be a supplemental rather than a prime backup for the moment.
Things might change after Microsoft proves that the Syntex backup and restore solution works consistently and reliably in different situations, we understand the true operational costs, and Microsoft expands coverage to include other workloads. In the interim, we await the chance to test the Syntex solution when it’s available.
The Microsoft 365 Kill Chain and Attack Path Management
An effective cybersecurity strategy requires a clear and comprehensive understanding of how attacks unfold. Read this whitepaper to get the expert insight you need to defend your organization!





You wrote: ” SharePoint Online stores protected files in an unencrypted form to allow services like indexing and search to work against the content.”
MSFT states encryption is used for SPOL. https://learn.microsoft.com/en-us/microsoft-365/compliance/data-encryption-in-odb-and-spo?view=o365-worldwide#encryption-of-data-at-rest
Yep, and I am correct. SharePoint Online can protect files with sensitivity labels. When SPO uploads protected files, it strips the encryption and stores the files in an unencrypted state to allow functions like indexing and DLP processing to work. Any access to a protected file causes SPO to encrypt it with Microsoft Information Protection. The page you refer to covers the file-level protection of SharePoint Online data rather than the file-level encryption I refer to when discussing issues with backup.