Office 365 for IT Pros, 4th Edition is continually updated with new information, changes and corrections. Updates applied to the Amazon Kindle version are available through your Kindle library after they are approved by Amazon.
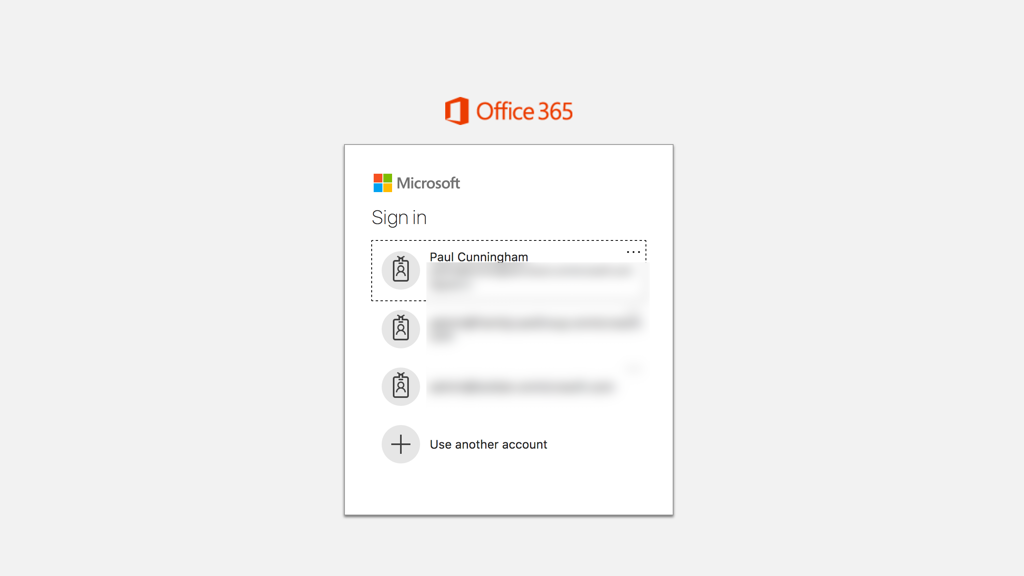
Microsoft gave us an early surprise in August with the unannounced rollout of a new beta sign-in experience. With no administrative controls available to suppress the opt-in notice, users were free to try the new experience and discover all of the errors and bugs that typically appear for beta software. Microsoft did eventually roll out fixes for the highest impact issues, and hopefully learned yet another lesson about communicating changes in Azure and Office 365.
Microsoft Intune continued to improve with full support on day 1 of the release of Android Oreo. As Intune continues to stay on the cutting edge of mobile developments, Microsoft has also announced the end of support for iOS 8.0 and Android 4.3 (or lower). A new version of the Company Portal app is due for release in the near future, and will only support iOS 9.0 or later. The older version of the app will remain available in app stores for a short period of time, but Microsoft encourages customers to ensure their end users are upgrading their mobile devices to avoid issues with mobile access to corporate data and applications.
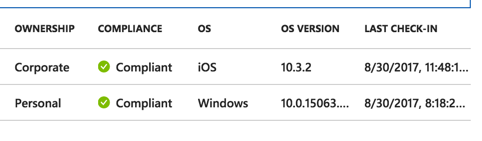
Microsoft has also rolled out macOS support for Azure AD/Intune conditional access policies. This capability is currently in preview, and has already turned up one bug with enforcement of password policies for macOS devices causing devices with non-compliance passwords to be reported as compliant until the user updates their password.
Intune’s role in software deployment got a big boost with the announcement of Office 365 ProPlus deployment capabilities. This is part of the Microsoft 365 vision, allowing Office 365 ProPlus click-to-run apps to be deployed to enrolled devices running Windows 10 Creators Update (and later builds, I assume). No word yet on whether the Teams desktop client will also be deployable with Intune in future. This also ties in with Windows Autopilot, allowing users to sign in to new devices with their corporate credentials and have them provisioned with software and configurations via Azure Active Directory and Intune. When you combine this with the focus these days on web-based applications, it’s getting close to the stage where computer rollouts are as simple as shipping new hardware directly to the end user.
The Intune team also announced support for multiple identities in OneNote for iOS, allowing Intune to differentiate between personal and corporate data stored in OneNote so that app protection policies can be enforced (e.g. preventing copying of corporate data to personal notebooks).
Office 365 Groups received a new feature that many customers have been waiting for. You can now define a Groups lifecycle policy that will automatically expire Groups that have reached the age (in days) that you specify. Expired groups begin a 30 day countdown before they are removed. Group owners are notified of the expiration by email and can “renew” a Group before it is removed. Group owners can also restore a removed Group if the miss the initial expiration notifications. You can define a lifecycle policy that targets all Groups, or specific Groups, allowing orgs to exempt any known long-running Groups from the expiration process.
Although this is a welcome feature for many customers, I am disappointed to see that it requires Azure AD Premium licenses for the administrator who configures the policy, as well as the users who are members of Groups targeted by the policy. Customers who are not willing to incur that cost will simply need to live with the sprawl of Groups that is occurring in tenants as users create Teams, Plans, and Outlook Groups. Furthermore, the expiration trigger is entirely based on the age of the Group, not the level of activity that is occurring in the Group. Activity is a difficult thing to detect right now. It’s possible that Groups that are no longer being used by humans could still be receiving emails or Teams channel activity from automated process such as Flow and the myriad of apps and connectors that can be integrated into Teams. Hopefully in future Microsoft will surface more reporting capabilities for administrators to be able to identify inactive Groups so that they can make informed decisions about which Groups to target with the expiration policy.
In other Groups news:
- Microsoft is rolling out a change so that newly created Groups will have unique mailNickname attributes. This change is not driven by any issues in the cloud, rather it is necessary to prevent collisions with mailNicknames for on-premises Active Directory objects when Groups write-back is enabled.
- Guest access to Groups can now be controlled by administrators using allow/block lists. Admins can define lists of domain names that are allowed or blocked from guest access invitations. This allows customers to enable guest access for the domains of trusted partners without opening up guest access to the world.
- Groups reporting has been enhanced with data about file activities in the SharePoint site associated with the Group.
In SharePoint Online, Microsoft is rolling out a change to the default external sharing configuration for site collections. For tenants that do not allow Groups to have external guests, SharePoint Online will not enable external sharing on new site collections by default. The external sharing configuration for existing site collections will not be modified by this change.
First Release customers are also getting new site theming options for SharePoint Online. Microsoft is making six color themes available that can be configured on a SPO site, and will apply to all pages in the site. At the upcoming Ignite conference they also plan to share more information about custom themes for SharePoint Online in future.
In other Office 365 news from August:
- Outlook for Android is getting support for Outlook add-ins, which Outlook, OWA, and Outlook for iOS already have. Outlook for Android is controlled by the same Outlook add-in policies as the other Outlook clients.
- The classic Service Health Dashboard is being retired. The new dashboard has been in effect for several months now and offers much better user experience, so it’s time for the old dashboard to be put away. However, development of the new dashboard seems to have stalled. Back in February I noted a roadmap item for email and text notifications to be added to the new Service Health Dashboard. They still haven’t appeared, and the roadmap item remains “in development”.
- Microsoft is retiring GigJam, an app that never made it out of preview. I never used it, though it does seem like a useful capability. Perhaps the learnings from GigJam will reappear in other Office 365 apps in future.
- The Message Center Weekly Digest Email preferences are being changed to stop using the alternate email address of administrative accounts. Admins will be able to define up to two additional email addresses to receive the digest email instead. I still prefer my own script for Message Center email notifications, but the change is an improvement. The original design of the email digest result in a bunch of unwanted emails to me from many different tenants, and for multiple admin and service accounts where my email happened to be the alternative email address.
- A problem with some Azure AD Connect automatic upgrades caused some instances to stop synchronizing at all. You can check the cause and solution here.


