If you are responsible for a Microsoft Exchange Server that is connected to the internet then you need to know what an open relay is.
In short, an open relay is an email server that is configured to accept mail from any sender and deliver it to any recipient. This is an undesirable configuration because it can be exploited very easily by spammers and other malicious users.
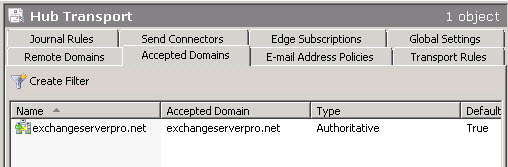
A properly configured Exchange server will accept mail sent from outside senders to recipients that are “known” or “local” to that Exchange server. In Exchange Server 2007/2010 this is configured in the Accepted Domains settings for the organization.
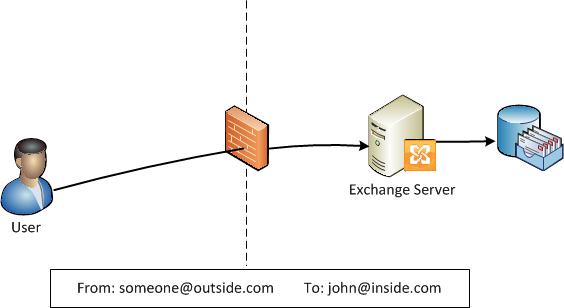
In other words, it is normal and expected that senders outside the organization can send email to recipients inside the organization. That email should be accepted and delivered by the Exchange server (assuming the recipient actually exists).
This may be slightly different in the case of shared SMTP namespaces and External Relay domains, but for the sake of this article we’ll focus on this simple example.
In comparison, a server that is an open relay would allow a sender from outside of the organization to send (or “relay”) emails to recipients who are also outside of the organization.

Clearly this is bad because a malicious person could send spam, phishing emails or malware via your Exchange server.

The most obvious risk here is that your Exchange server is used by spammers to exploit others. Another concern is how much of your network and server resources this type of exploitation can consume.
But a more serious concern is that it can lead to other mail systems blocking mail that is sent from your server. This can happen in several ways, such as your server being listed on a blacklist such as Spamhaus, or other email systems performing an open relay test on your server and blocking it when it fails the test.
In their default configuration Exchange Server 2007/2010 are not open relays. However through operator error they could become an open relay. If you have any concerns about your Exchange server possibly being an open relay you can test it by going to Abuse.net and entering your Exchange server’s public IP address or DNS name (ie your MX record) and running the test.
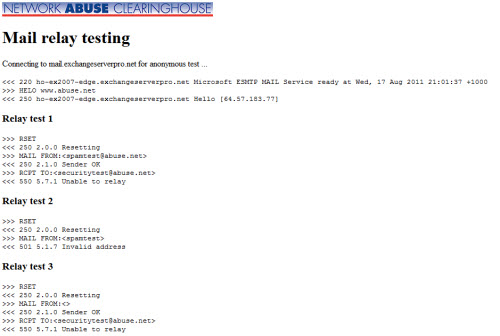
I run this test multiple times on any Exchange server deployment that I’m involved in, or any time a change is made to internet-facing servers. If you’ve never run an open relay test on your own server this may be worth considering.



Hi, I know this is an old thread, but somehow our Exchange 2019 server has become an open relay. Is there a way to test to see what receive connector the open relay is referring to? Or what (mis) configuration can I check on my connectors?
Thanks for your help
Pingback: My E-mail appears as spam | The 7 major reasons | Part 6#17 - o365info.com
Pingback: Testing telnet open relay | Words. Thoughts.etc
Just a quick note to say thanks. I’ve used your site several times to get answers to what should be straightforward problems. Sadly, attempting to use the forums or even just to search Microsoft’s resources almost always ends up in a long and rambling thread between two people on a forum that, after literally a dozen screens or more of back and forth you come to the end and can’t for the life of me figure out what the answer was. At least here I get a simple answer to a simple question. Thanks. Much appreciated.
Pingback: Email Fundamentals: What is an Open Relay? « MidThought's
Pingback: Email Fundamentals: What is an Open Relay? – Exchange Server Pro | promote website|online promotion|online promotion|website promotion:qmmt.info supply