Reading the headers of an email message can reveal very useful information for Exchange Server administrators who are diagnosing problems.
Email message header information includes details such as the route that the email took (ie which email servers were involved in the transmission of the message), who sent it, who it was addressed to, and whether the email message was scanned for spam or viruses.
This is useful for both internal and external email messages. As just one real world example, I often need to use email message header information to diagnose message delivery delays.
How to Access Email Message Header Information in Outlook
Each version of Microsoft Outlook lets you access the email message headers, but they do it in slightly different ways.
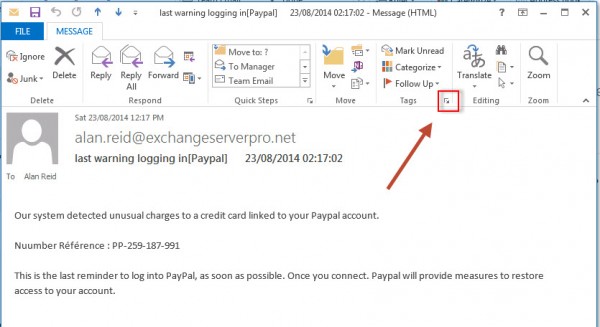
To read the email message headers in Outlook 2013 click on the arrow next to Tags in the ribbon menu.
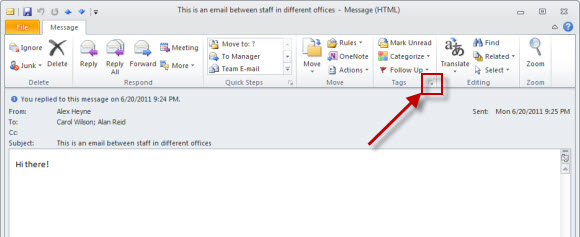
To read the email message headers in Outlook 2010 click on the arrow next to Tags in the ribbon menu.
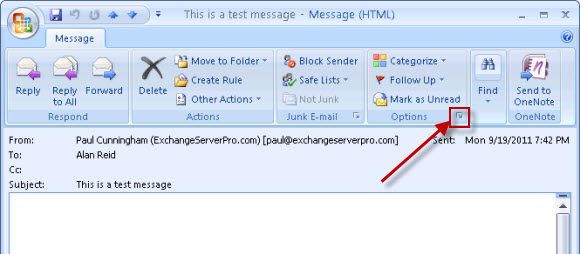
To read the email message headers in Outlook 2007 click on the arrow next to Options in the ribbon menu.
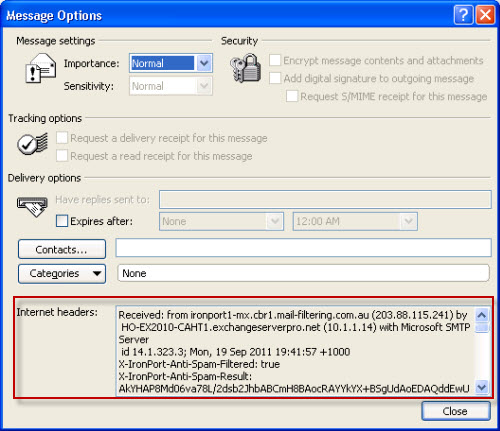
The message options will appear with the email message header information towards the bottom.
Reading Email Message Headers in Notepad
First let’s take a look at how difficult it actually can be to read the raw message header information that you get out of a message in Outlook. If you copy the message header information into Notepad will look like a complete mess.
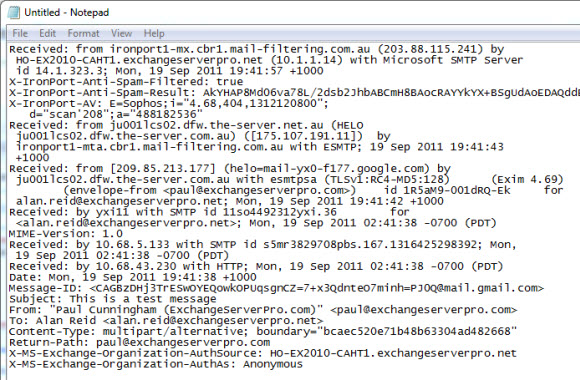
Even though it is is quite messy and difficult to read you can still see useful information in the message headers. First there is the basic information about the email message itself.
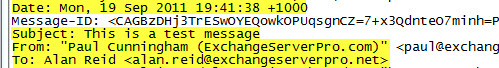
Then there are the email servers that the message passed through on it’s way to the destination. To follow these in order start at the bottom and read upwards.
These lines are generally in the following format:
Received: from servername (IP address) by servername (IP address) with MTA-name; timestamp
When a message passes over several hops this can get a bit confusing to read, especially when the timestamps are all from different time zones. Fortunately there are some useful tools you can use to present the email message header to you in a much easier format to read.
Reading Email Message Headers Using Header Analyzer Tools
Here are three online tools you can use analyze email message headers. For demonstration purposes I’m using the message headers from a spam email message that I recently received in a mailbox in my test lab.
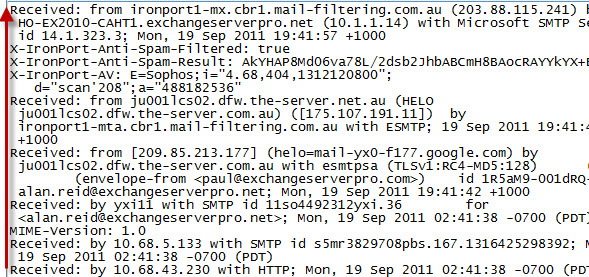
Microsoft Remote Connectivity Analyzer
The Microsoft Remote Connectivity Analyzer includes a Message Analyzer tool. Paste the message headers into the field provided and click Analyze headers to produce the report.

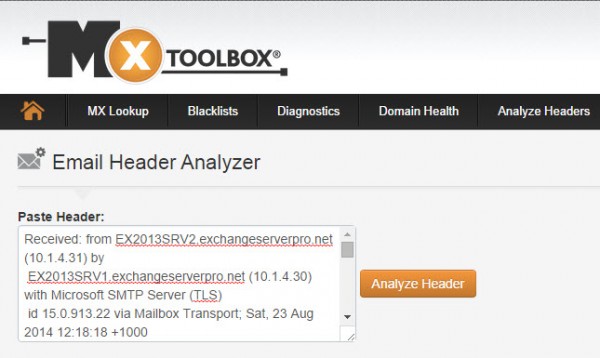
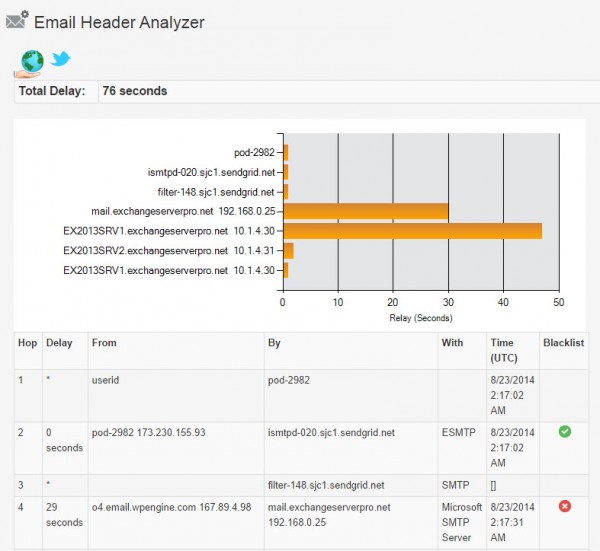
MXToolbox
MXToolbox also has a section of the website for analyzing message headers. Again simply paste the header information into the field provided and you get a nice, graphical report out of it.
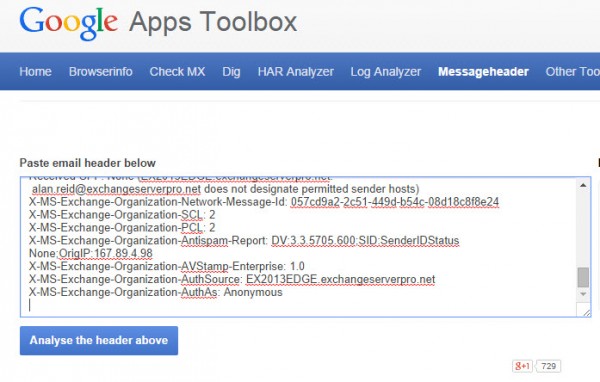
Google Apps Toolbox
Finally there is the Google Apps Toolbox which includes a Messageheader analyzer tool that has similar functionality to the others.
Summary
As you can see reading email message headers provides you with a lot of very useful information for diagnosing email problems. You can retrieve email messages easily using email clients such as Outlook, and then use any of the third party message header analyzer tools to produce an easy to read report from that message header data.




Is there a way to determine the sending Exchange server’s version from the header?
If they excluded this kind of information in the E-mail-Header it is not possible to determine the exchange version.
I’ve tried all 3. Google totally fails saying “We were not able to recognize email headers in the text you entered.” The other two “worked”, but didn’t give me what I want. At the end of my source, there is this:
Content-Type: image/jpeg;
name=”image004.jpg”
Content-Transfer-Encoding: base64
Content-ID:
/9j/4AAQSkZJRgABAQEAeAB4AAD/2wBDAAoHBwkHBgoJCAkLCwoMDxkQDw4ODx4WFxIZJCAmJS
It goes on a good while as the junk data is some form of the JPG file identified. I cannot find the image004.jpg on “TomsMainPC” which is the PC on which the email was retrieved. I need to see what the image looks like. What header analyzer will interpret the JPG data into a viewable image? This was a “sent” message. Furthermore, I am not happy that “TomsMainPC” or the image therefrom were sent with the email, and I want to prevent it.
Hi All,
Come across an interesting issue when deploying a Hybrid scenario with the following inbound route to and EXO mailbox:
Internet –> 3rd party Cloud Scanning –> On-Prem –> EXO
in this, On-Prem to –> EXO treats the email as safe flagging the X-Forefront-Antispam-Report with SCL:-1 and SFV:SKI and of course the other headers as:
X-MS-Exchange-Organization-AuthAs: Internal
X-MS-Exchange-Organization-SCL: -1
So as such, the destination for the user in EXO Junk Email Filtering Block list is ignore and thus the email goes into the users Inbox. Is this a known flaw with Hybrid?
Thanks.
I suspect your Cloud Scanning -> On-Prem hope is flagging the mail as Internal, which can be caused by the configuration of the receive connectors that are handling the inbound mail to the on-prem org. Did you create custom receive connectors for that or are you just using the default connectors with no modifications?
Would be nice if the message analyzer went further and decoded the anti-spam codes and other codes that Microsoft puts in to see which rules were ran, why a message was sent to Quarantine or the attachment failed a check, etc.
I’m sure if you provide that feedback to Microsoft they’ll consider it.
Hello,
Is there a way to retrieve header information in EMS or logging on Exchange Server (non email client)?
Found a solution: https://gallery.technet.microsoft.com/office/How-to-export-Email-7f63a63c. Just replace the path Microsoft.Exchange.WebServices.dll for Exchange 2013.
No. Headers are stored in the message.
Hello,
Is any way to determine from the e-mail headers what device sent an email if the account is on microsoft exchange?
No, that info is not stored in the headers.
header parsing, and mail-server-hops received from … received from … may it be parsed on EXCHANGE SERVER?
i want to create FILTER based on suspicious mail-from servers included in mail delivery path
pisibli power-shell script on Exchange server?
Nice article. But don’t forget about other important parts of message header, like antispam tags and other useful information.
Pingback: Reading email headers using apps for Outlook | Bhargav's IT Playground
There is a MessageHeaderAnalyzer app that can be imported into Outlook 2013 and just a 1 Click drop down on the app – it gives the header info with a neat view; (App uses testexchangeconnectivity.com’s Message header Analyzer in the back-end)
Same App for Exchange 2013 mailbox will be available in Outlook and OWA.
Nice article
Thanks.
Adam
How can I determine when an email was created? My boss stated that she sent an email to the staff on a Thursday but the staff didn’t receive until Friday. I believe she is lying. The sent time indicates it was sent on Friday at 4:09 and it was received by me on Friday at 4:09. Is the scenario she describe possible.
Hey Paul !
Nice article- sorry for posting a question on and old thread but have you ever noticed the contents of the headers and their values when the Cache on option is selected ?
In Outlook 2007 If I turn on cache (Tools / Account settings / Change / Check the Use Cached Exchange Mode box) email headers in the SENT box are not populated, with cache off the header contains emailid information.
Do you have any clues as to why ? – it is causing a problem with a tool we use here.
I can’t reproduce the behaviour you’ve described.
Funny – that is what the vendor is telling me too …
We can reproduce the behavior on any account here.
Hi,
mxtoolbox has a tool for analysing headers that could be quite useful.
http://www.mxtoolbox.com/EmailHeaders.aspx
Hope this helps
Sean
In Outlook 2010 the headers have been moved to the ‘File’ Tab of an email opened in its own window, select ‘File’ and then under the Info section click Properties’ to view the message headers.
hope this helps
Hi Paul,
Nice Article.
Check out the Email Message Header Parser i wrote for the Hey Scripting Guy Blog, it parses email header and calculates delays between different hops.
Part1 : http://blogs.technet.com/b/heyscriptingguy/archive/2011/08/18/use-powershell-to-parse-email-message-headers-part-1.aspx
Part2 : http://blogs.technet.com/b/heyscriptingguy/archive/2011/08/19/analyze-email-headers-with-powershell-part-2.aspx
thanks
Thiyagu
Hey that looks really useful, I’ll have to put that to use at work 🙂