New Year. New Challenges. New Security
As time advances, new threats, and challenges develop across the technology spectrum. Microsoft 365 tenants might have a dedicated individual to manage security for the organization, or security might just be one of the multitudes of tasks assigned to the tenant administrators. In either case, it’s wise to take the time to set some goals for 2023 to improve Microsoft 365 security and make your tenant harder for attackers to compromise.
As Microsoft says in its ten immutable laws of cybersecurity, “Not keeping up is falling behind.” That’s why it’s important to look at infrastructures like Microsoft 365 annually to identify areas where improvements can be made. Another of Microsoft’s laws is “Attackers don’t care.” In other words, attackers will keep on trying new ways to compromise tenants. Tenants must continually up their security game to stay ahead of new attack vectors.
You might already be progressing in the five areas described below. If so, that’s great. A secure tenant is a happy tenant. But the likelihood is that most tenants can improve their identity security posture, so treat this as a prompt to review and improve your arrangements.
TEC Talk: Five Things Microsoft 365 Security Administrators Should Do in 2023
Don’t miss Tony Redmond’s free TEC Talk on this topic on March 23rd at 11:00 am EST.
Increase MFA Usage and Dump SMS Challenges
Microsoft has done its best to remove a major source of account compromise (basic authentication for email protocols) from Exchange Online. Combined with authentication policies, tenants should be able to deny attackers the opportunity to reap a rich harvest of account information gained through attacks like password sprays. It would be nice if organizations then enforced multi-factor authentication (MFA) to make probing even more difficult.
In 2019, Microsoft said that MFA blocks 99.9% of account compromises. Even so, the curious thing is that the percentage of Microsoft 365 accounts protected by MFA is not growing as strongly as it should. According to Alex Weinert, Microsoft VP for Identity Security, only 26.64% of Azure AD user accounts are MFA-enabled (September 2022). Possibly even worse, only 34.15% of Azure AD accounts holding administrative roles are MFA-enabled. Microsoft says that enforcing Security Defaults for more tenants will offer protection to another 60 million accounts. That’s good, but it’s even better when tenants take hold of their own destiny and insist on MFA for all accounts. It’s the single biggest step an organization can take to improve its security posture.
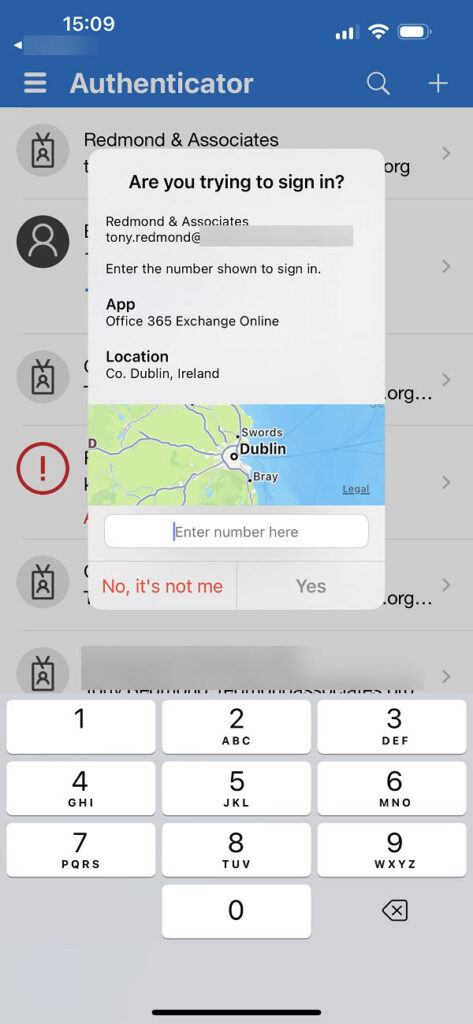
And when you insist on MFA, don’t let people use the relatively insecure forms of MFA like SMS challenges (subject to an increasing number of attacks). Instead, use Windows Hello, FIDO2 keys, or the Microsoft Authenticator app. Microsoft has hardened the Authenticator app (Figure 1) recently with features like number matching to lessen user fatigue from MFA challenges (Microsoft will enforce number matching for everyone on May 8, 2023 – make sure your users are prepared). A side-effect is losing support for Authenticator on WatchOS devices, where it’s hard to satisfy secure MFA challenges like number matching.
You don’t have to use Microsoft’s multi-factor authentication functionality, as other solutions are available on the market. Select your preferred solution and make it your goal to exit 2023 with all user accounts protected by MFA.
Take Control of Connections
After blocking unwanted authentications with MFA, the next barrier is access control imposed by conditional access policies. It would be great if Microsoft made conditional access policies available to all, but they require Azure AD Premium P1 licenses. This isn’t usually an issue for larger enterprises because the license is part of bundles like Enterprise Security and Mobility, but it’s often the smaller tenants that need the most protection.
Conditional access policies limit access to resources according to conditions set in policies. For instance, SharePoint sites that hold confidential information might be blocked to all except those who sign-in from inside the corporate firewall on a managed device. Another policy might block access to resources unless the user authenticates with a strong MFA method like the Authenticator app. Microsoft continues to add new capabilities (conditions and filters) to give organizations maximum flexibility in handling connections. That’s a good thing. It also points to the need to pay attention to what Microsoft does in this space.
Conditional access policies are a powerful method to control who gets access to what. The downside is that it’s easy to lock yourself out or create a maze of complexity with multiple policies that make conflicting demands. If you start your conditional access policy journey in 2023, start simple and add conditions over time as you become accustomed to working with policies and users cope with their requirements.
Protect Confidential Information
Attackers are wily opponents, and it is possible that they might navigate past the barriers erected by MFA and conditional access. If they do penetrate an account, limit the amount of information they can access with sensitivity labels. Relatively few organizations use sensitivity labels today, but the number is growing thanks to the investment in information protection technology made in Microsoft 365 over the last three years. In particular, the click-to-run, online, and mobile versions of Microsoft Office now include native (inbuilt) support for sensitivity labels, as does the paid-for version of Adobe Acrobat. The Edge browser can also read protected documents, and there’s a growing sense of maturity around the information protection ecosystem.
If users leave unprotected documents in SharePoint Online sites or send them as email attachments, anyone who can access those documents can access their content. Sensitivity labels stop this happening by insisting that anyone who attempts to open the documents has the assigned right to do so. If not, the documents remain inaccessible. People can see their metadata (like the title), but not what’s inside protected Word, Excel, or PowerPoint files.
In 2023, it would be nice if more organizations embraced sensitivity labels and started the planning process to introduce the technology. Don’t attempt to launch sensitivity labels without planning: it won’t work. Figure out how to use labels effectively and how to train users to protect information, and then run a test over several months with a representative set of people to discover if additional work must be done before a full launch. That’s enough for 2023.
Consider Security During PowerShell Upgrades
PowerShell developers who work on Microsoft 365 automation have their work cut out in 2023 because Microsoft will deprecate the Azure AD and Microsoft Online Services (MSOL) modules in June 2023 (the license management cmdlets from these modules stop working at the end of March 2023). At much the same time, Exchange Online is removing support for Remote PowerShell connections.
When updating scripts to use the Microsoft Graph PowerShell SDK, Graph API requests, or considering how to access Exchange Online mailbox data, consider taking the following actions:
- Eliminate any insecure credentials stored in scripts or files. Instead, use Azure Key Vault to hold credentials or use certificate-based authentication. If you use Azure Automation to run scripts, consider using managed identities.
- The permissions model used by the Graph is very different from the all-powerful do-anything approach often taken by PowerShell modules intended for administrative use. Make sure that your code uses the least permissions possible and audit apps to make sure that this happens.
- Use the Exchange Online RBAC for Applications feature to limit app access to mailbox data.
The last thing you want is to leave any tasty titbits in code waiting for an attacker to discover and exploit after they’ve got through MFA and conditional policies. Keep erecting barriers!
Master Audit Data
Microsoft 365 generates lots of audit data. The question is what use you make of that data. You can be passive and only look through audit data when something bad happens or take an active approach to analyzing and understanding what’s in the data. In October 2022, Microsoft’s cybersecurity DART team discussed how they use audit data for forensic investigations of issues like compromised tenants. It is possible for any tenant administrator to access and use the same data to highlight possible anomalies for investigation. For example, attackers compromised a tenant by planting a malicious app to send spam. That attack depended on being able to assign Graph permissions to the app after creating it in the tenant. App permission assignments are auditable events, and the data captured by Azure AD was available to the administrators, if only they cared to look – or better again, use automation to periodically check for similar events.
Many organizations take the audit data generated by Microsoft 365 and put it in a SIEM like Microsoft Sentinel or Splunk to retain the data for longer than the 90 days allowed by Office 365 E3 licenses and to take advantage of the more developed search and analytical tools available in the SIEM.
I have two calls for action relating to audit data in 2023. First, make sure that you know what information the major workloads (Exchange, SharePoint, Teams, and Azure AD) capture in the unified audit log and how to search the log with PowerShell. Second, acquire at least a working knowledge of the Kusto Query Language (KQL) so that you can interrogate the data stored in Microsoft Sentinel. Although you can depend on searching the internet to find the KQL queries you need to make sense of the logs assembled in the SIEM, the best idea is to learn KQL basics and make sure that you can construct and run moderately complex queries. Just enough to realize when something might be wrong. If that time comes, you’ll be able to act faster to secure a problem and fix the effects of any intrusion. If the organization doesn’t use Sentinel, make sure that you’re capable of interrogating the SIEM for evidence of malpractice.
TEC Talk: Five Things Microsoft 365 Security Administrators Should Do in 2023
Don’t miss Tony Redmond’s free TEC Talk on this topic, March 23rd at 11:00 am EST.
Always More to Do
Because of the size and scope of Microsoft 365, there’s obviously much more that administrators should review in terms of tenant security. For example, Microsoft will deprecate Exchange Online client access rules in September 2023. If your tenant uses client access rules to restrict user access to client protocols, it’s time for a rethink. Microsoft wants to focus on what it regards as more intelligent and resilient protection, such as Azure AD continuous access evaluation, but sometimes a straightforward block imposed by mailbox settings to stop accounts using protocols like IMAP4 and POP3 is enough.
One thing’s for sure. Ongoing threats and evolving attack vectors will keep Microsoft tenant administrators occupied for the foreseeable future. Establishing barriers, ongoing monitoring, and attention to detail are the only sure ways to limit exposure and prevent compromise.
The 2023 edition of the Microsoft 365 Security for IT Pros eBook is now available to help guide administrators to achieving better security for their tenants.





Hi, Tony!
Slight correction slipped in;
https://learn.microsoft.com/en-us/azure/active-directory/authentication/how-to-mfa-number-match
Number matching is postponed to May 8, 2023 according to the docs. Questioning of this date is definitive but we’ll see 🤓
Odd. That’s what I see in the post. Maybe some odd caching is going on as I know that I updated this text after Microsoft announced that they were pushing things out…
And, 3rd party backup!?
While I understand the need of CloudAlly employees to advocate for third-party backup, I am not so enthusiastic.